Allow Connections to Proxy in Microsoft Azure¶
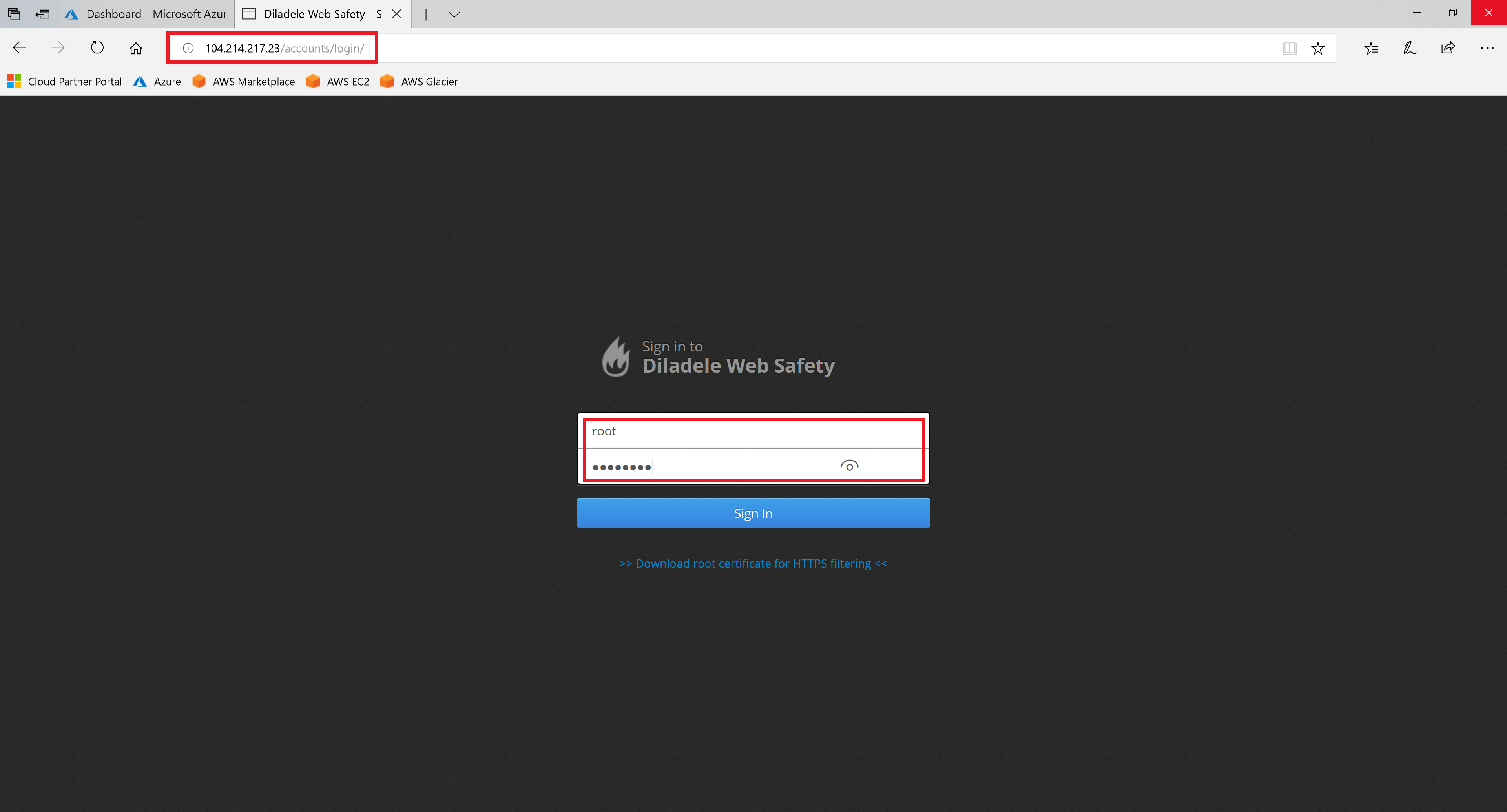
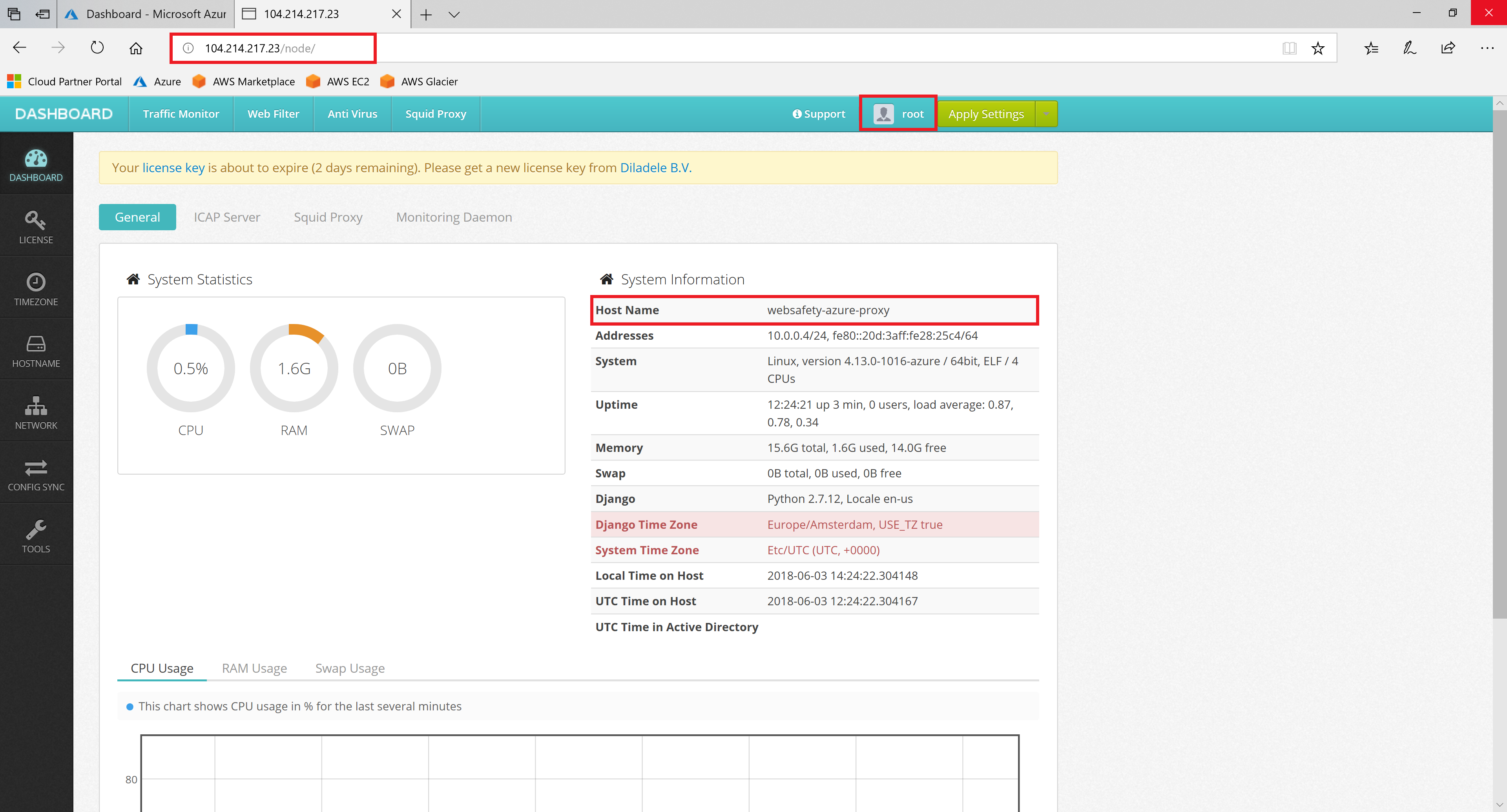
Good, now we have Azure deployed instance of Web Safety web filter integrated with Squid proxy. Open the browser and navigate to IP address of the running virtual machine (port 80, protocol HTTP). You should see the Admin Console UI of Web Safety. Type default root and Passw0rd credentials to see the dashboard.
Important
It may happen that at the time of installation the trial license that is built into the installer has already expired. In this case get the free trial license.pem file from support@diladele.com and install it as explained in article How to install the license key?
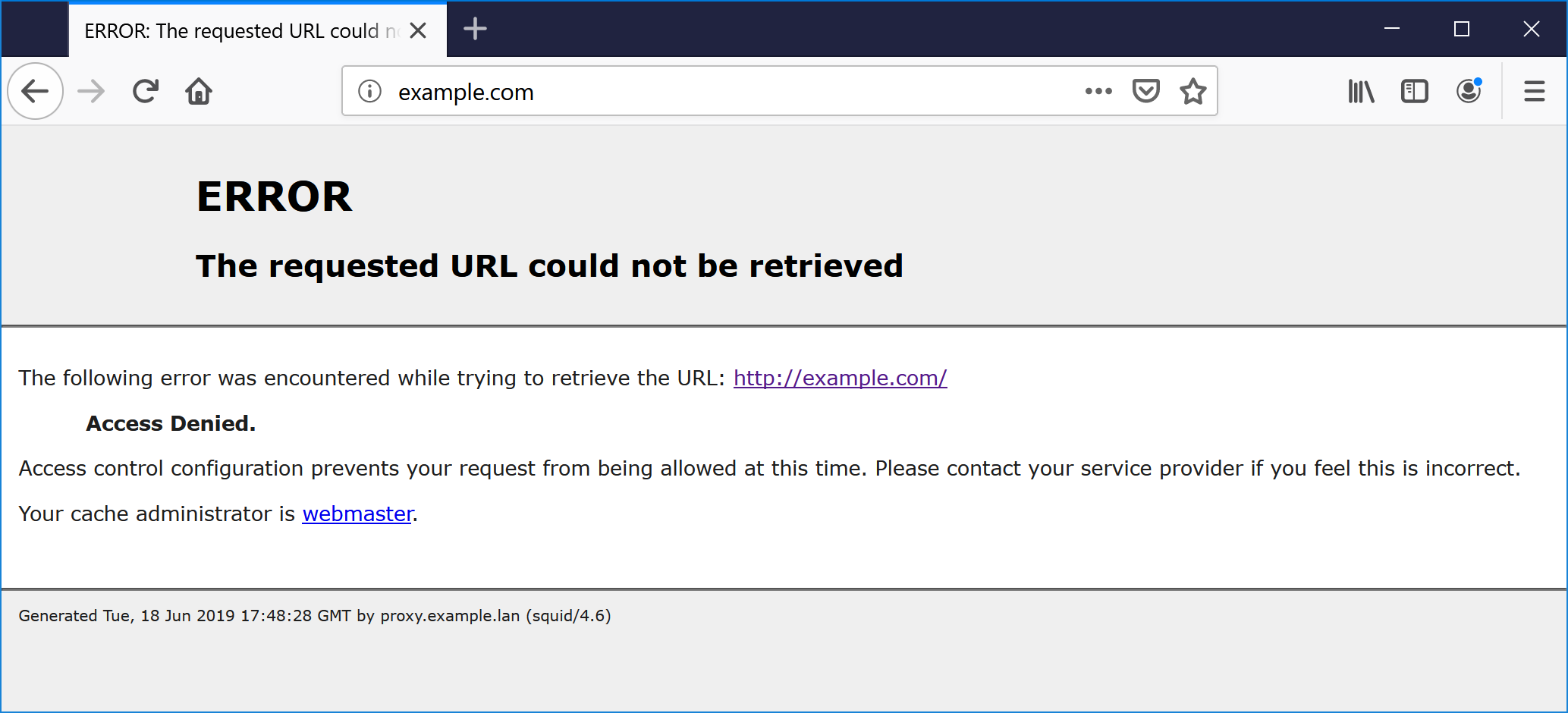
By default proxy allows connections from internal LAN IP address ranges only (addresses like 192.168.1.0/24). When our browser is set to talk to cloud proxy its visible IP address will be public (set by your ISP provider) and thus will be denied. Typically the following reply page will indicate a denied access:
ERROR
The requested URL could not be retrieved
The following error was encountered while trying to retrieve the URL: http://example.com/
Access Denied.
Access control configuration prevents your request from being allowed at this time.
Please contact your service provider if you feel this is incorrect.
Your cache administrator is webmaster.
Generated Tue, 18 Jun 2019 17:48:28 GMT by proxy.example.lan (squid/4.6)
There are two possible ways to solve this problem.
Way 1. Allow connections from your IP only (and use firewall incoming rules)¶
If you have a static public IP address set by your provider, then it is a good idea to limit the incoming connections to the proxy only from this public IP address using the security group firewall rules in the Microsoft Azure.
After that, open the Admin UI of Web Safety, navigate to Squid Proxy / Settings / Default ACLs and type the following directives:
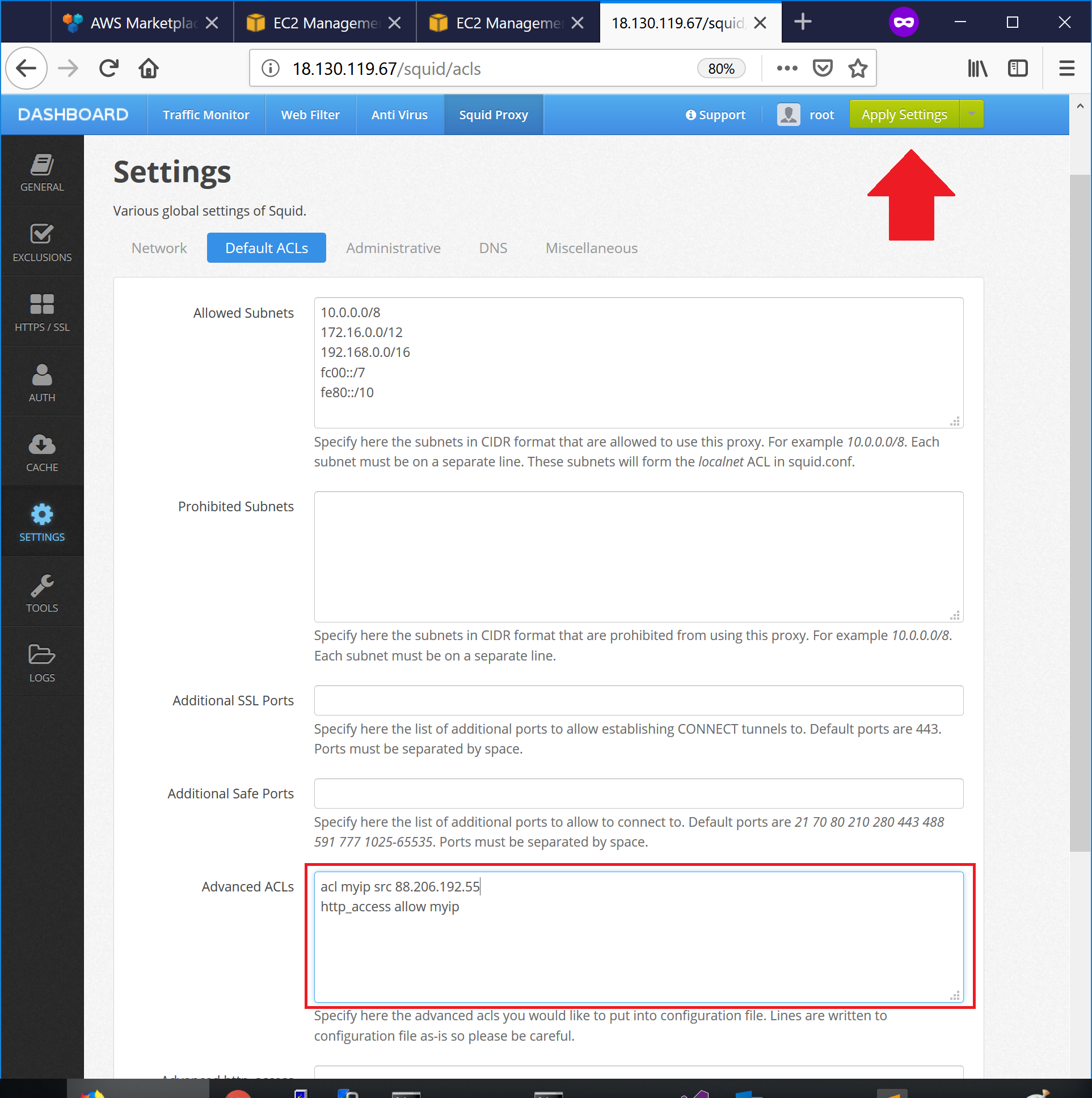
This will allow connections to the proxy from a given public IP address only.
Way 2. Require all connections to authenticate¶
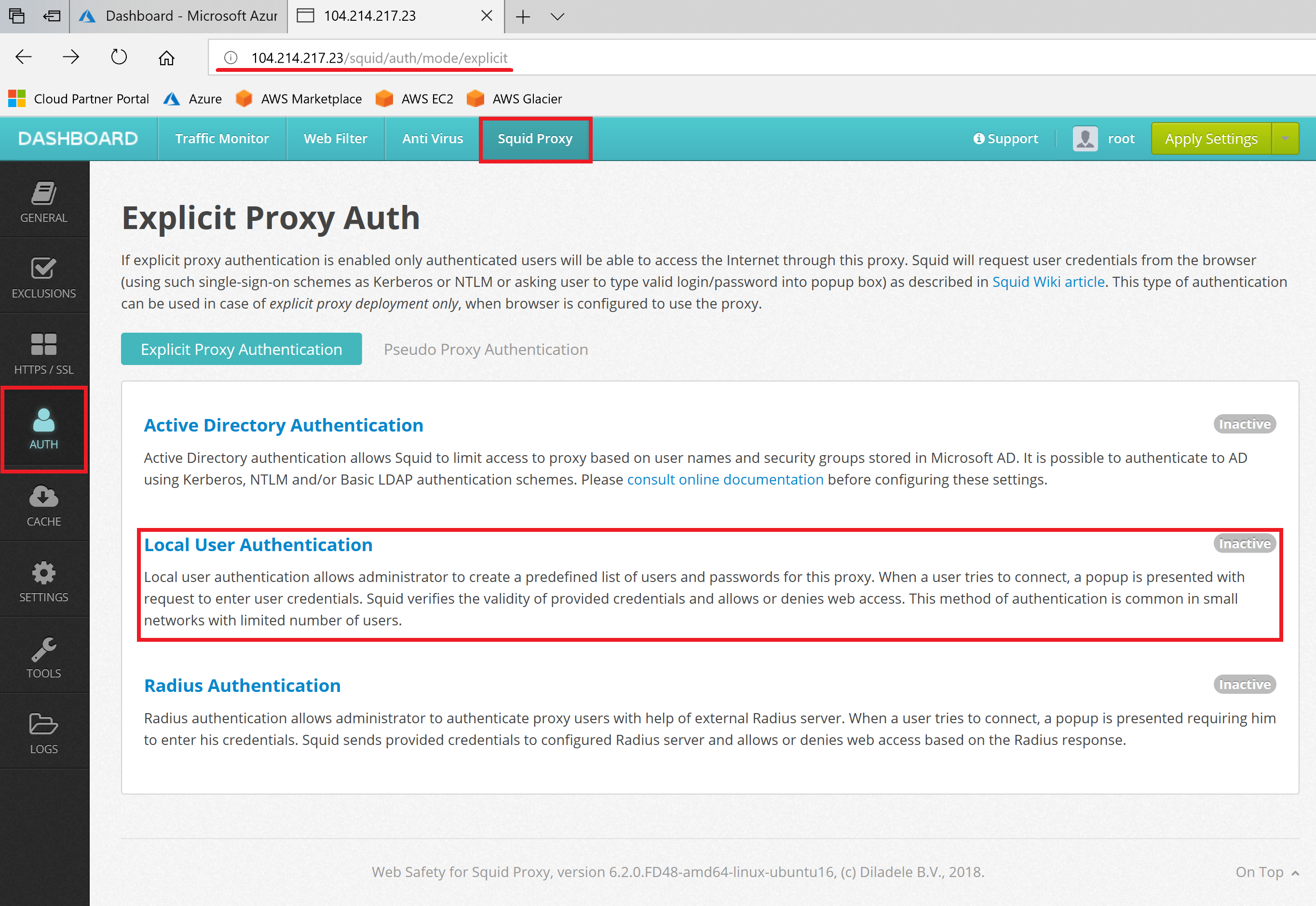
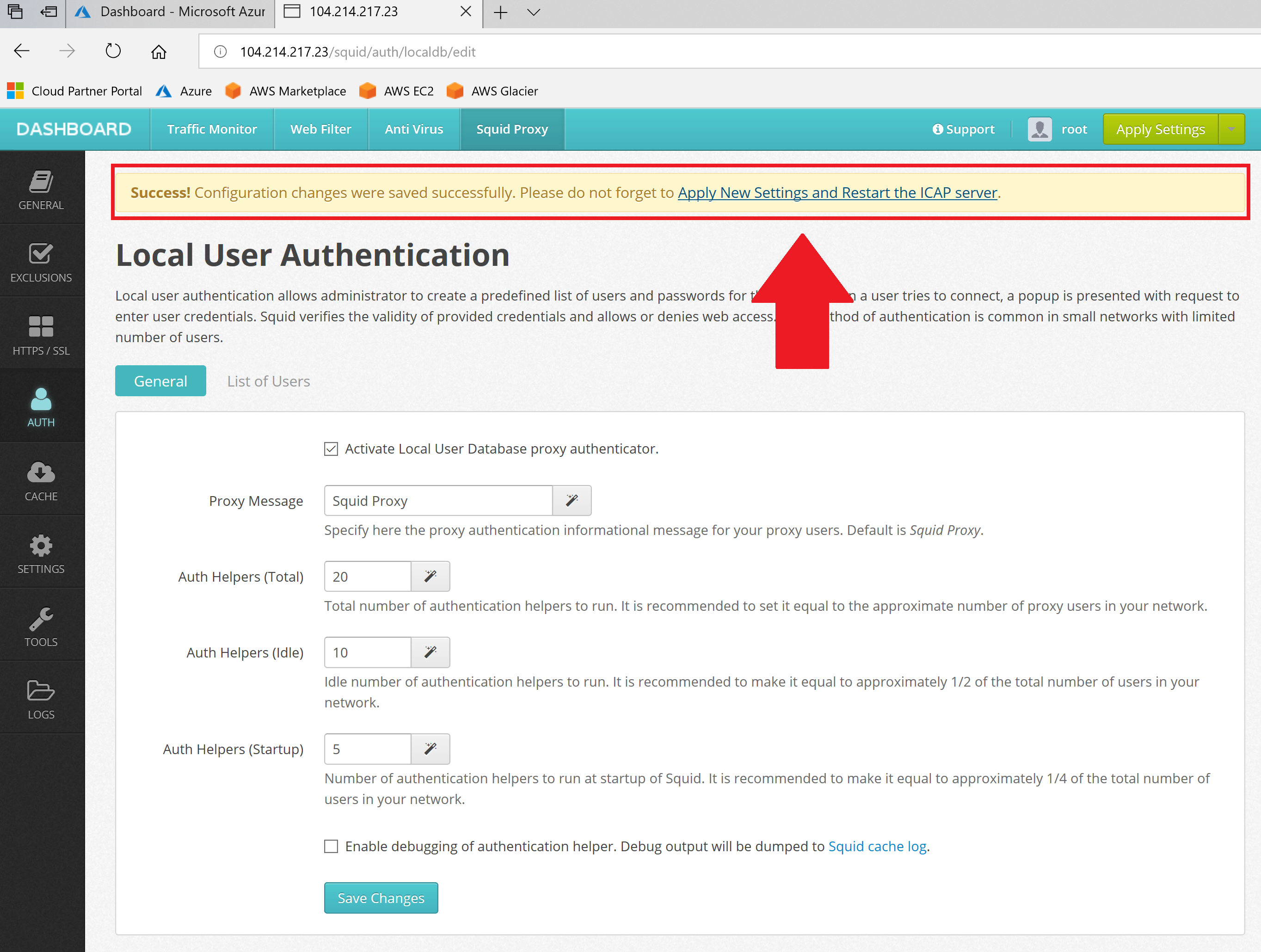
To enable basic proxy authentication, open Admin UI of Web Safety and navigate to Squid / Auth / Local User Database authentication.
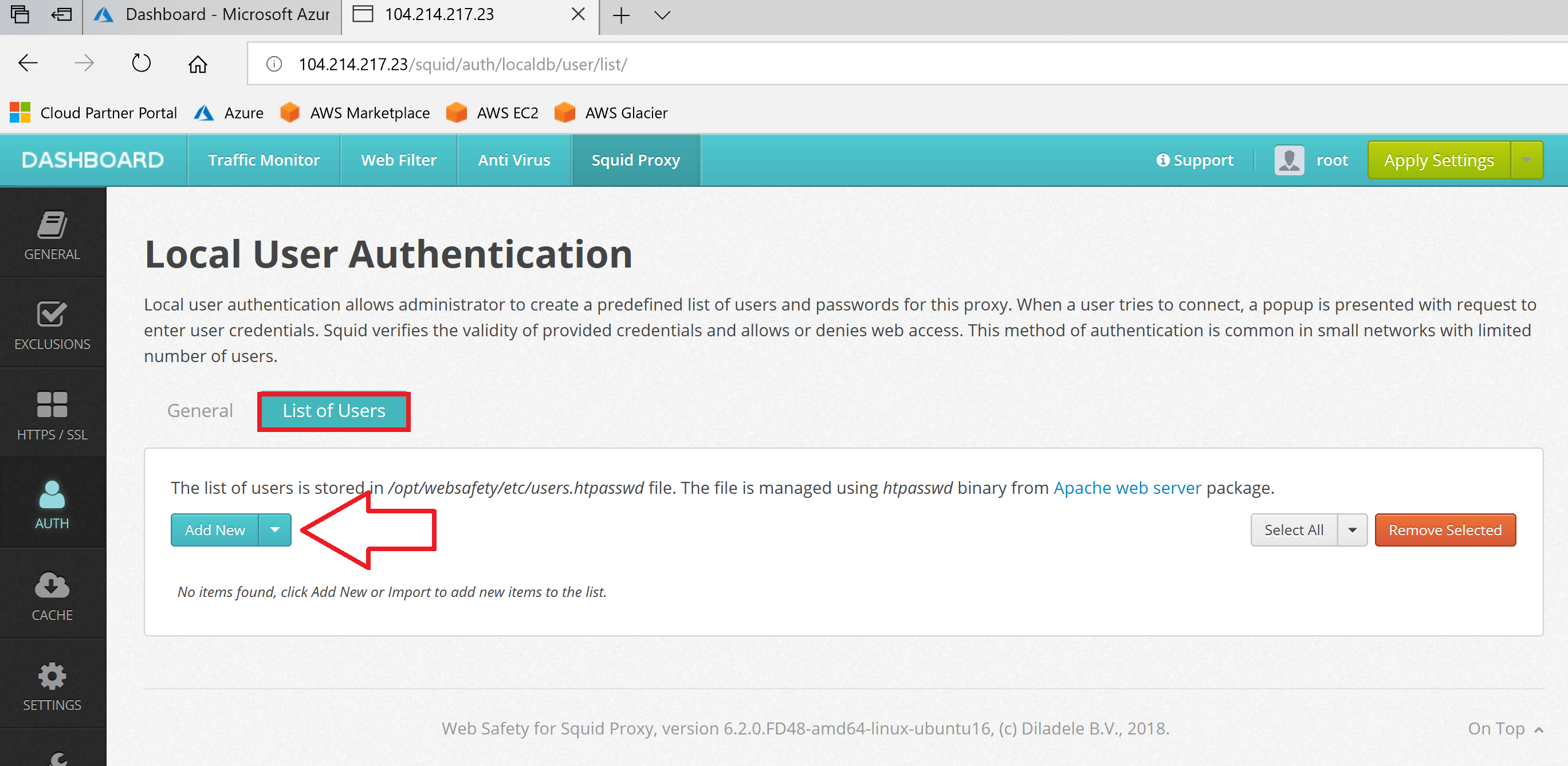
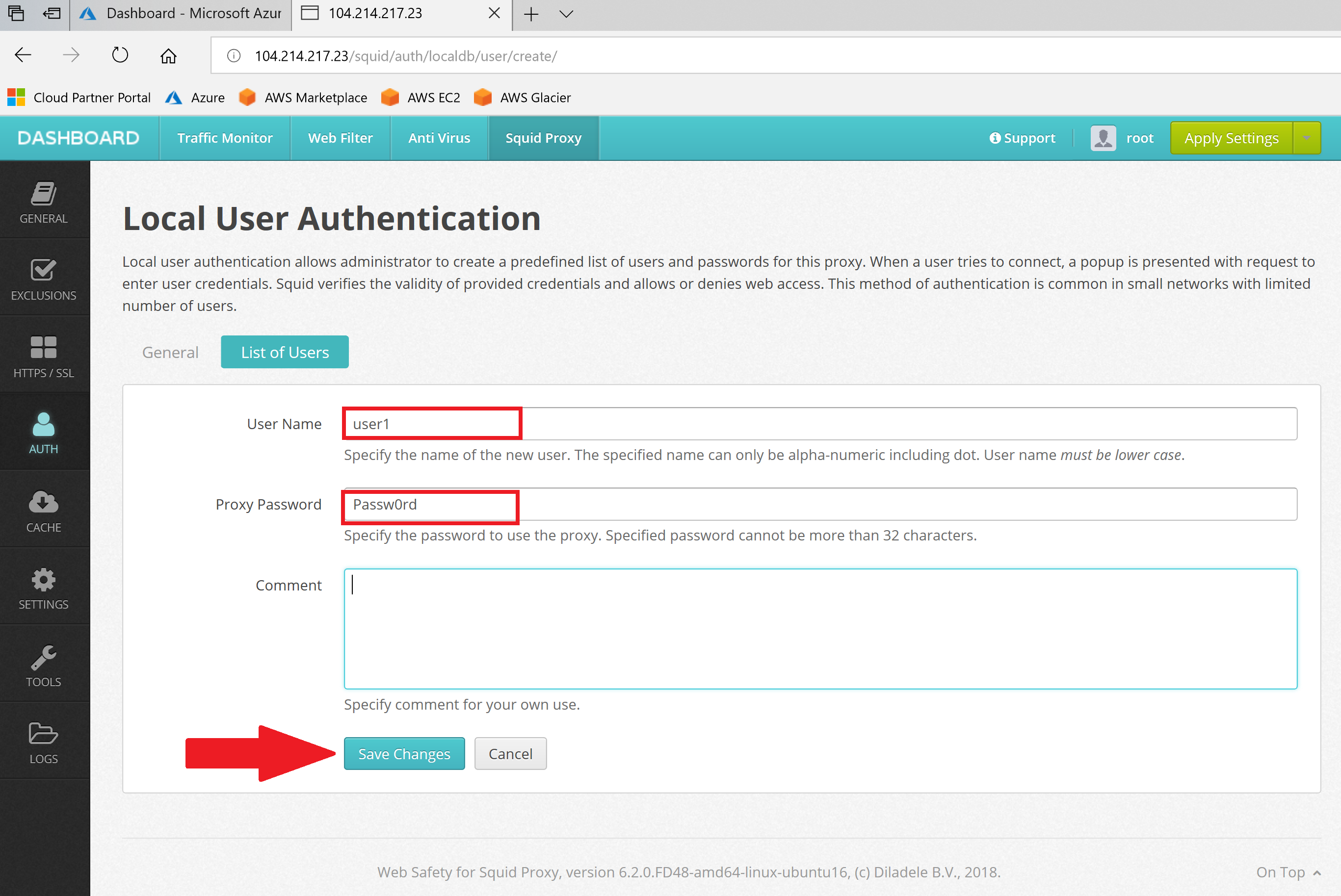
Click the List of Users to see the list of users and add a new user to the local database. Provide any user name and password.
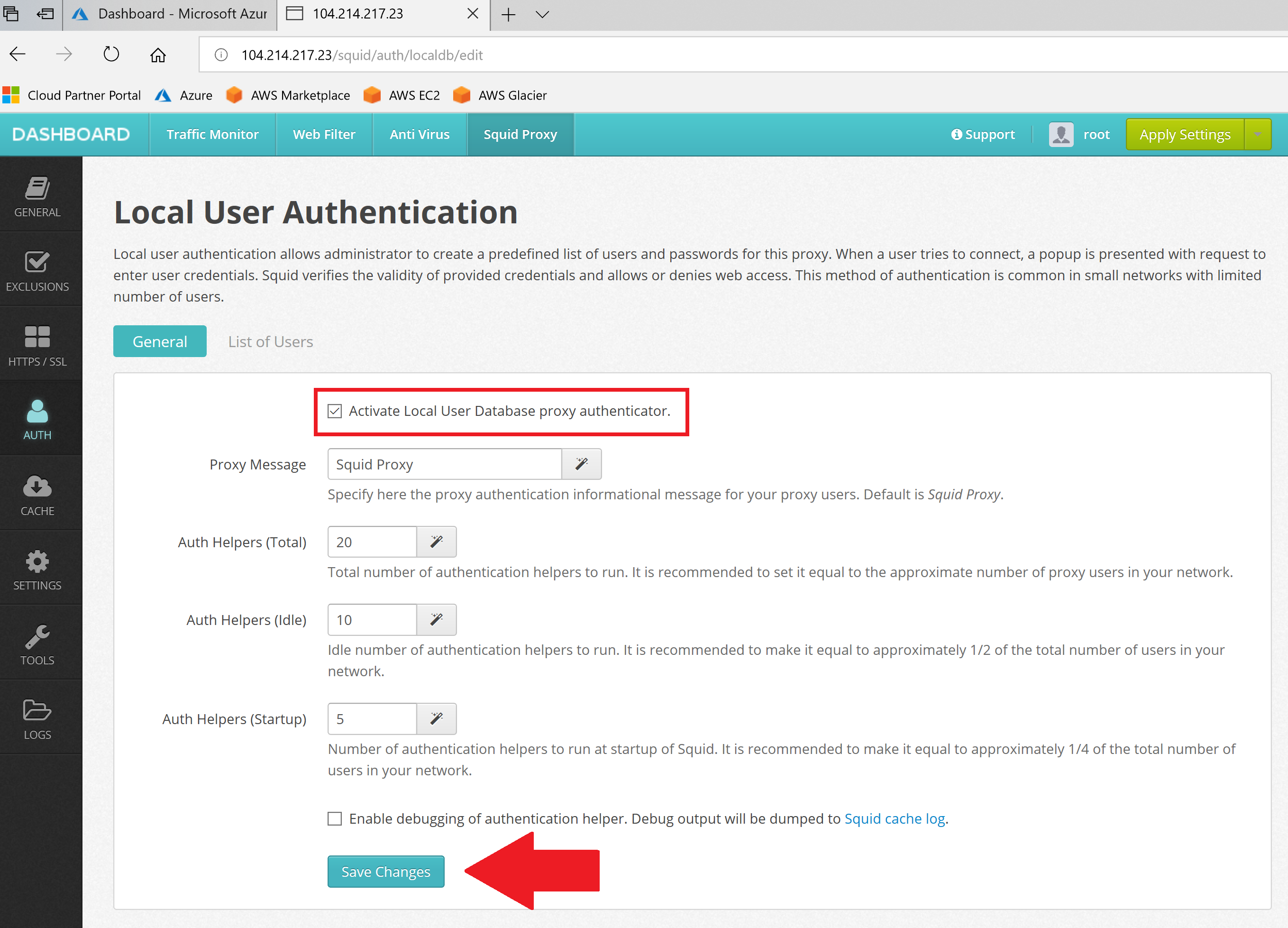
After user is added, select Activate authentication, click Save settings and reload configuration by clicking on Save and Restart.
Now we need to configure browser to use our proxy.