LDAP groups as Members in Web Filter Policies¶
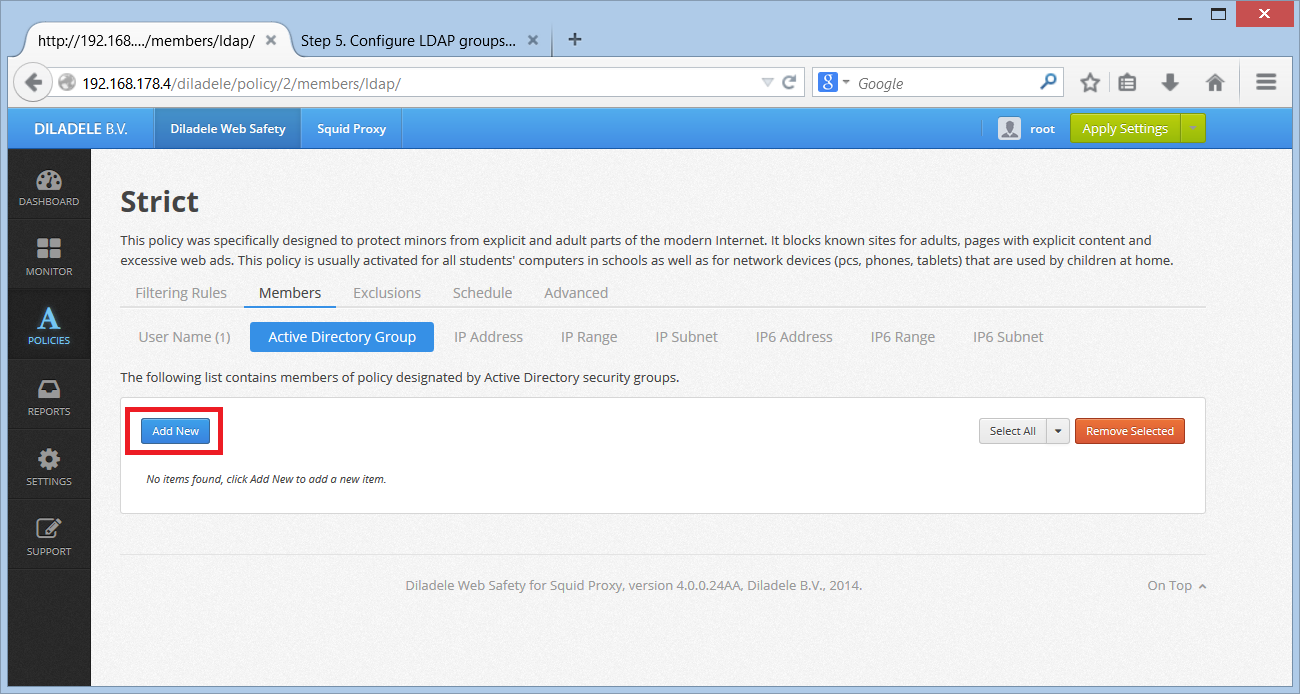
The Web UI of Web Safety allows selecting security groups from Active Directory as members of filtering policies. Select the desired policy and click the policy members tab. Add new LDAP group by clicking Add New button to the right.
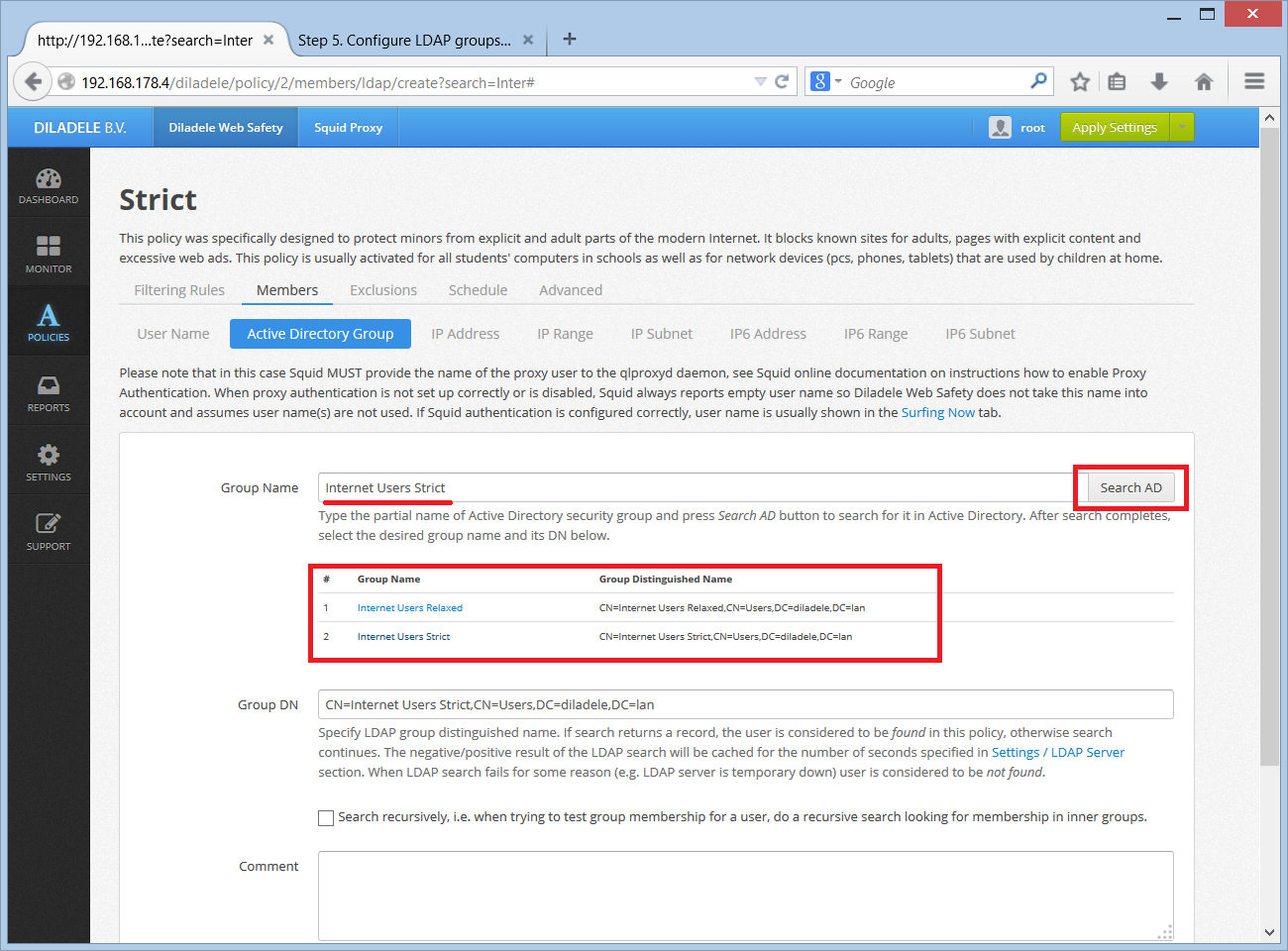
In the Add Group window fill in the name and distinguished name (DN) of the security group. It is possible to search for specific group using the search button on the right.
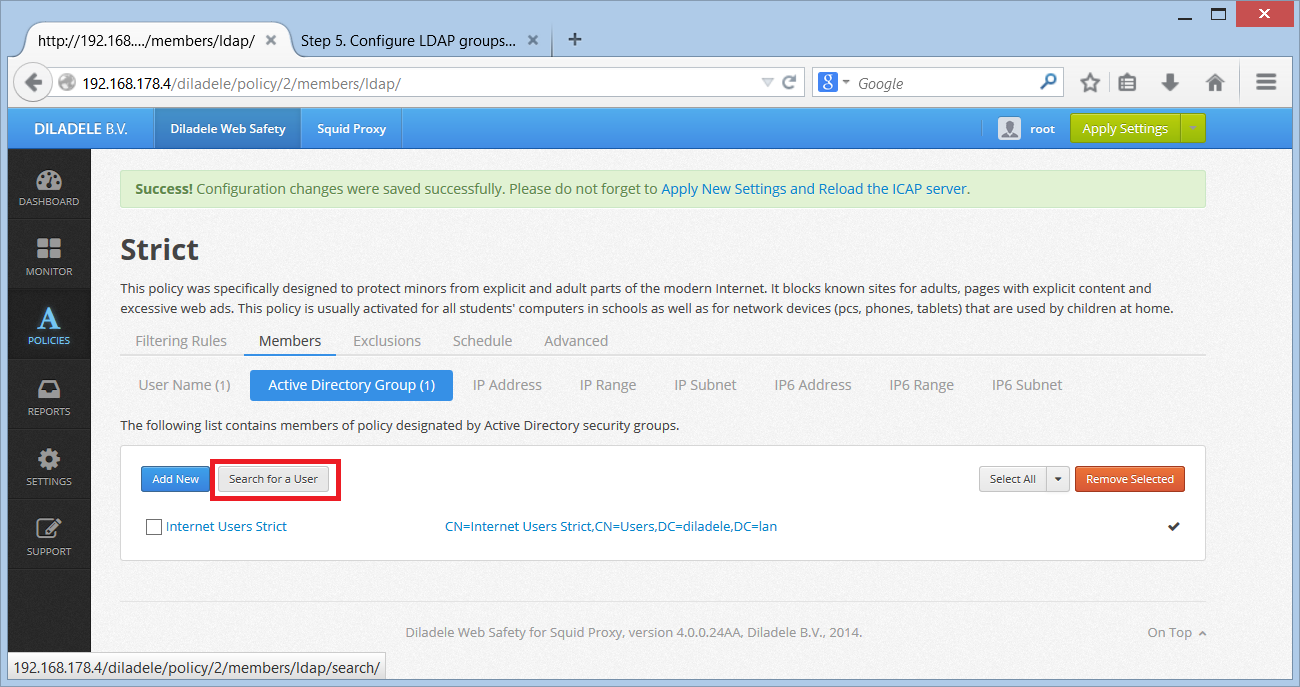
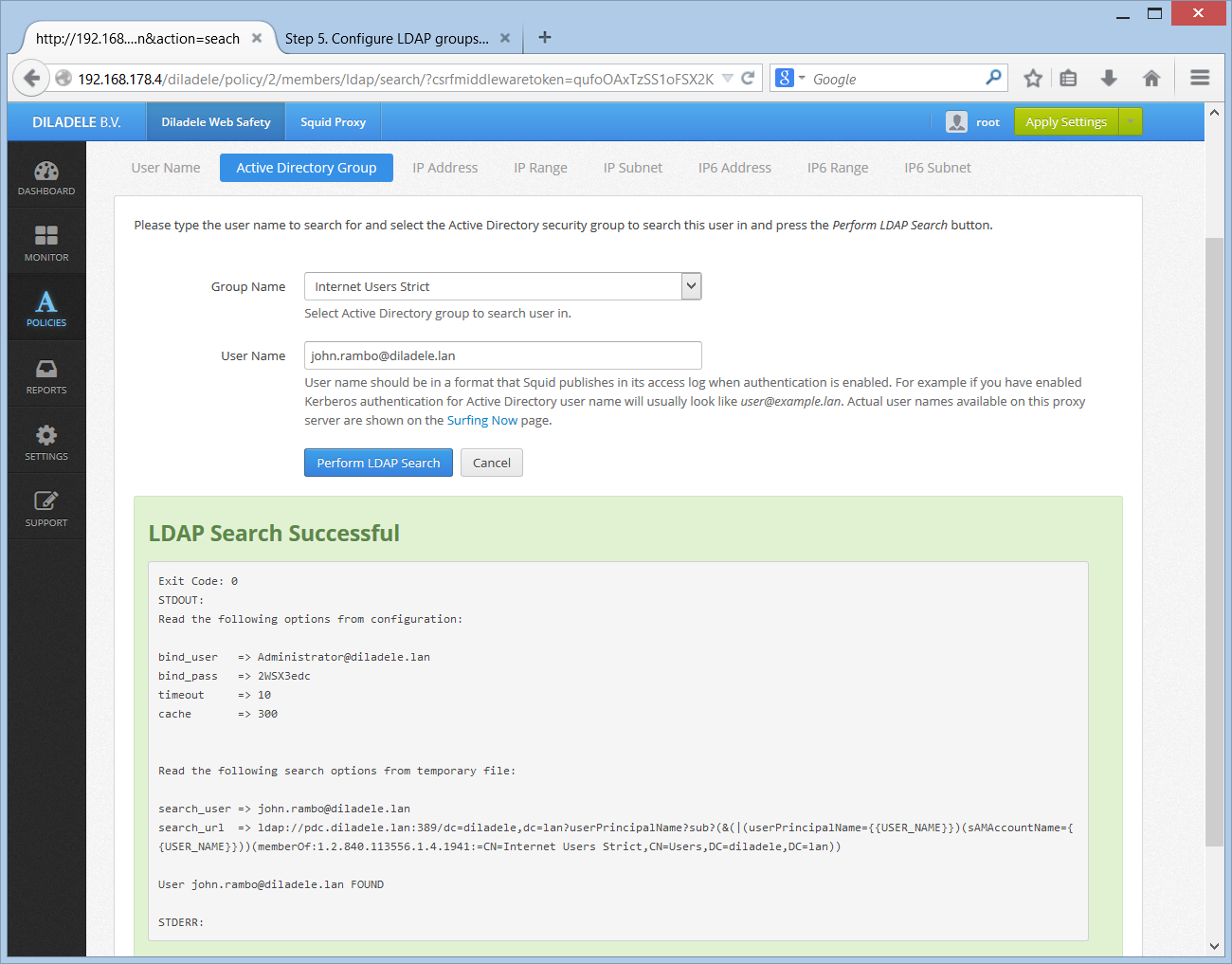
When LDAP group is selected, it is recommended to click the Search for a User button to see if the known user can be found in the selected group. To do that fill in the user name (e.g. user or user@example.lan) and see if LDAP module of Web Safety correctly identifies the user as belonging to the group.
then
Click Save and Restart to apply the configuration. After restart Web Safety will be able to automatically check if given user is a member of selected LDAP group and automatically apply correct filtering policy.
Required Search Permissions in Active Directory¶
Note that after a user connecting to the proxy has been successfully authenticated, the proxy needs to find out the list of Security Groups that user is a member of. To perform this search the proxy binds to configured LDAP servers using squid user that we have created on the Step 3 of this guide. It is very important to ensure that this squid user has enough permissions to read the memberOf attribute of any given user in your Active Directory environment.
To check that all required permissions are in place, try searching for some user in Active Directory as shown on the following screenshot. Be sure to verify that the user is found and memberOf attributes are indeed populated correctly.
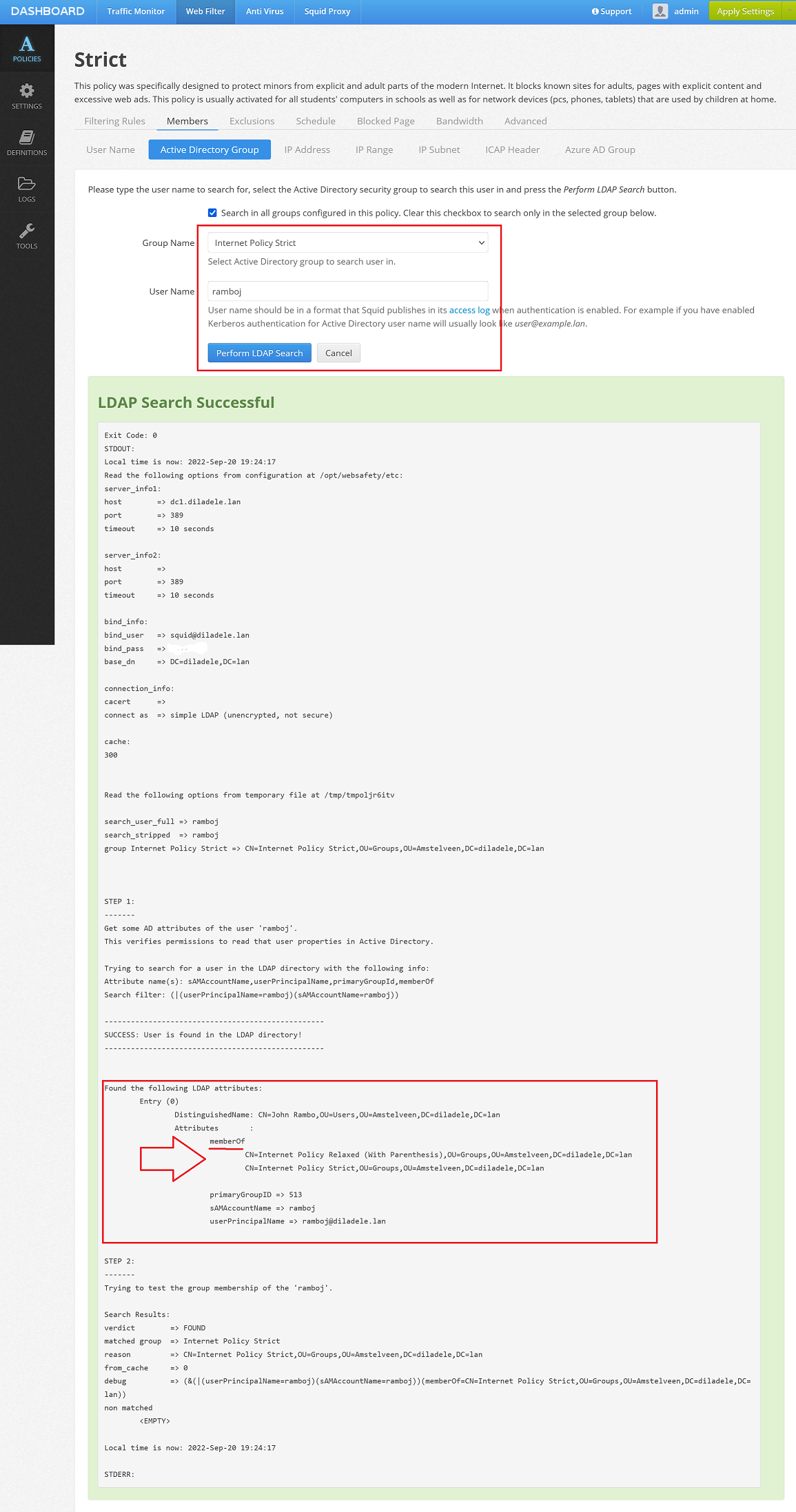
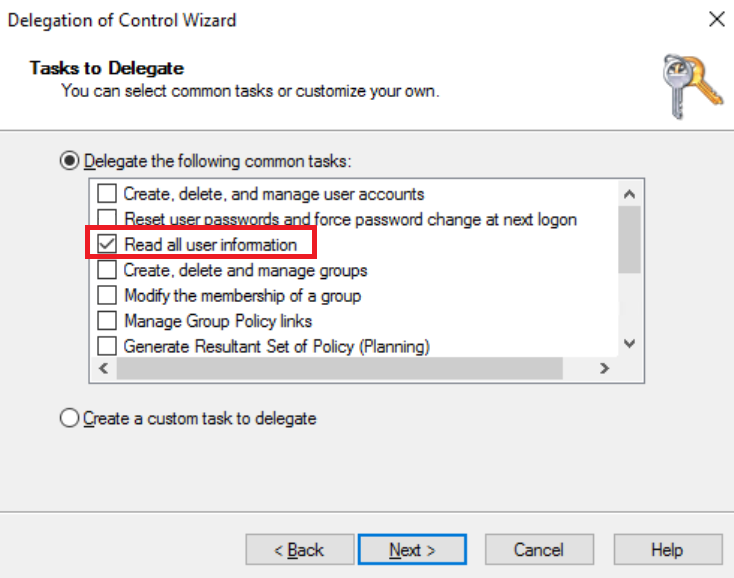
In default deployments of Active Directory the squid user usually has all required permissions to do the search correctly. However in some hardened Active Directory deployments you would need to manually give the squid user the correct permissions to do that search.
Please see the article at https://activedirectorypro.com/delegate-control-in-active-directory/ for more information. It is known that the “Read all user information” permission works well in this case.