Proxy Authentication¶
Web Safety can be configured to require connecting users to authenticate themselves. There are three major ways to enforce proxy authentication.
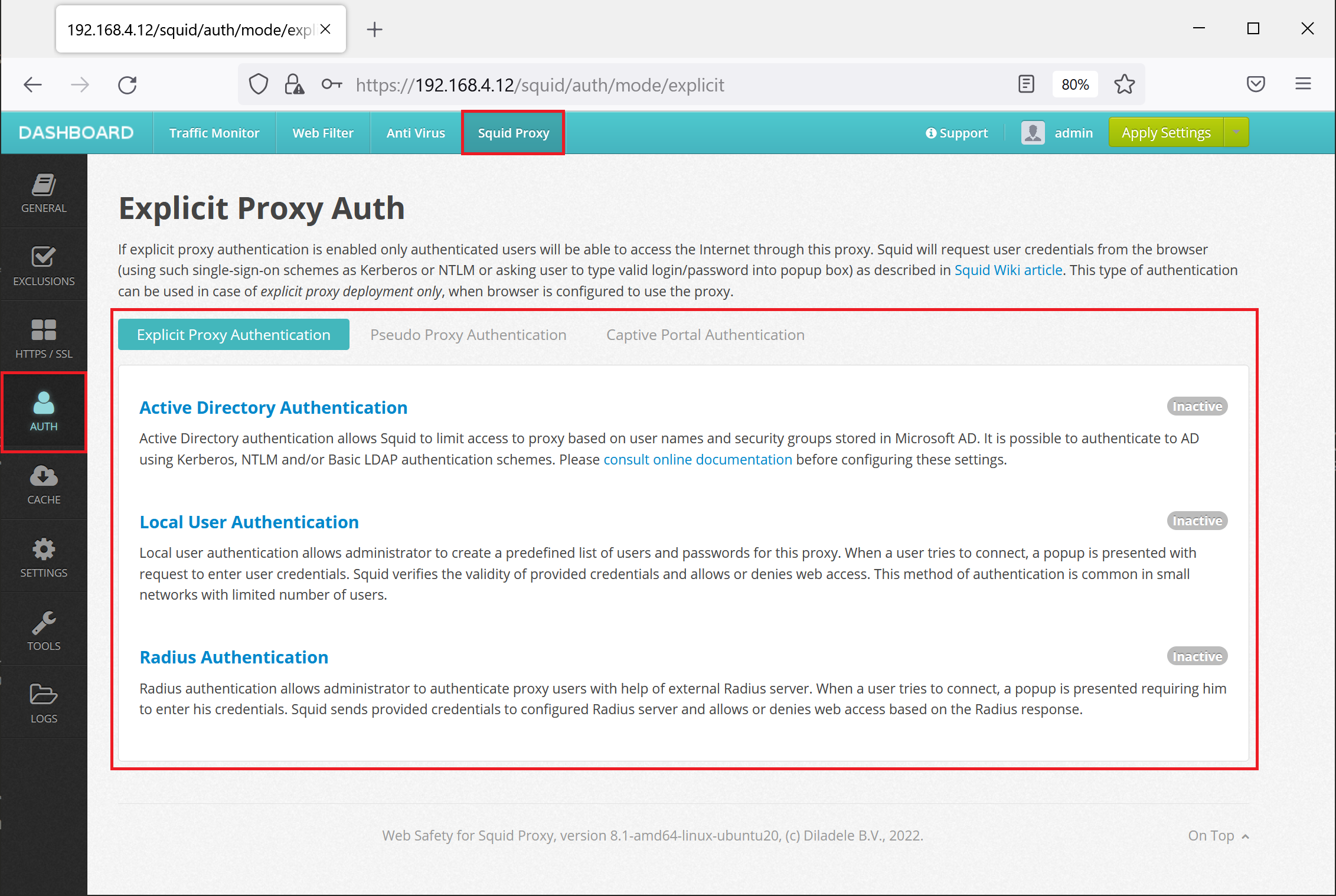
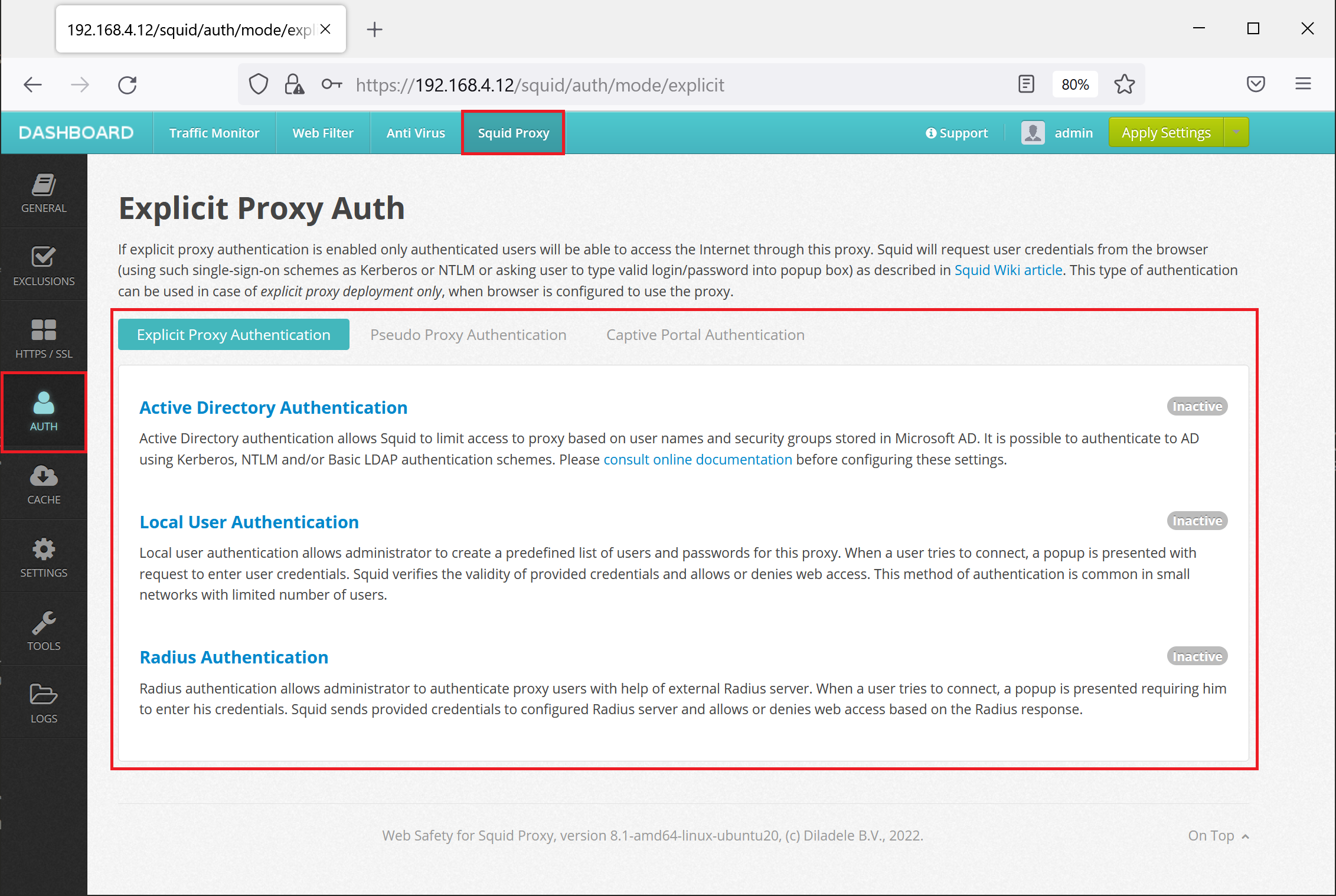
The proxy authentication is configured in Squid / Auth node in the Admin UI.
Web Safety can be configured to require connecting users to authenticate themselves. There are three major ways to enforce proxy authentication.
The proxy authentication is configured in Squid / Auth node in the Admin UI.