Install Squid and Web Safety¶
Our router will run Squid proxy for transparent interception of HTTPS and HTTPS traffic and Web Safety for URL and content filtering.
Warning
It is not a good practice to install any additional components on the router. Much better way to deploy the filtering proxy in your network is by using a separate virtual appliance as explicit proxy. If transparent deployment is a must, it would also be better to use the separate virtual appliance and redirect the traffic to it using policy based routing.
Follow the installation manual for RHEL 9 (Rocky Linux) to install these components (../../administrator_guide_develop/install/redhat9/index). Just run the scripts in the core.redhat9 and ui.rpm one by one as root.
Switch port of Admin UI¶
Integration of Web Safety UI and Apache was done automatically by the installer, but in case of transparent filtering proxy some more steps are required. Normally Admin UI of Web Safety runs on port 80 but this port will be used by Squid for transparent interception, so we need to change the port Admin UI listens on.
Ensure you do not have file /etc/httpd/conf.d/welcome.conf. It is default page of non configured Apache that may interfere with Admin UI.
Change
Listen 80in file /etc/httpd/conf/httpd.conf on approximately line 45 toListen 8000. Save the file.Change
<Virtual Host *:80>in file /etc/httpd/conf.d/websafety.conf to<Virtual Host *:8000>. Save the file.Restart Apache web server by running
systemctl restart httpd.
Do not forget to allow connection to Admin UI through the firewall by running the following commands.
firewall-cmd --permanent --zone=public --add-port=8000/tcp
firewall-cmd --reload
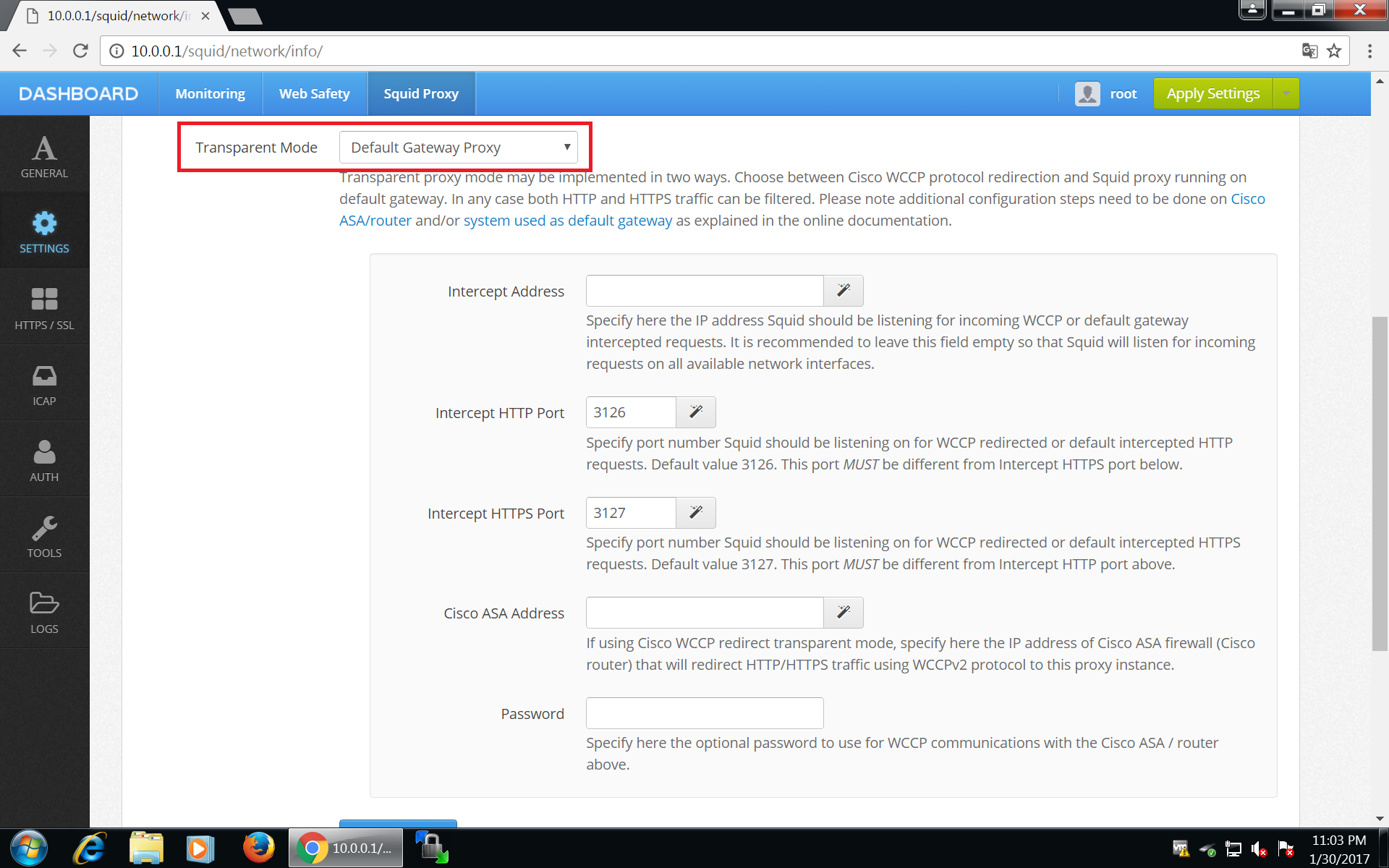
Enable Gateway Mode¶
To make Squid listen on transparently redirected ports 3126 and 3127, login into Admin UI of Web Safety at http://10.0.0.1:8000 , click Squid / Settings / Network and select Default Gateway Proxy transparent mode as shown on the screenshot below. Do not forget to click Save and Restart afterwards.
Note
After clicking Save and Restart, Admin UI will generate required http_port and https_port directives in /opt/websafety/etc/squid folder. These will look something like
# port configuration
http_port 3128 ssl-bump generate-host-certificates=on dynamic_cert_mem_cache_size=4MB cert=/opt/websafety/etc/myca.pem
http_port 3126 intercept
https_port 3127 intercept ssl-bump generate-host-certificates=on dynamic_cert_mem_cache_size=4MB cert=/opt/websafety/etc/myca.pem
IMPORTANT: please note, ports 3126 and 3128 are prefixed with http_port directive and port 3127 is prefixed with https_port directive.
Restart your proxy box now and continue on the next step.