Post Deploy Configuration¶
After initial deployment we will need to configure some additional settings before we can integrate our proxy with Google Workspace.
Set Proxy Domain Name¶
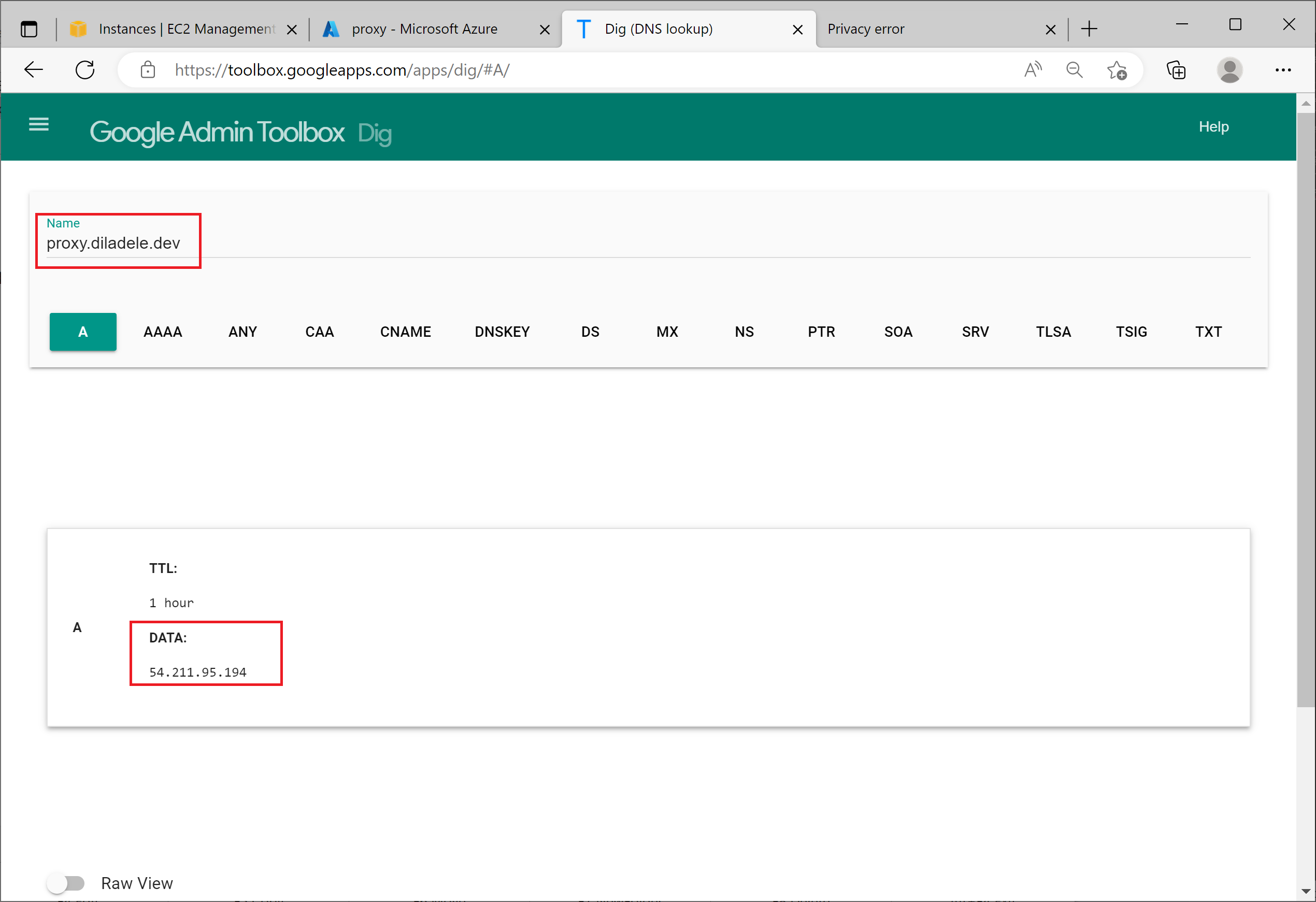
First thing to do is to assign a proxy.diladele.dev domain name to our virtual machine. How this is done largely depends on your DNS provider and as we use Azure DNS management for our development lab it is quite simple - just add the A record for proxy in diladele.dev DNZ zone.
Checking with Google DNS toolbox gives us the following.
Arrange the Certificate¶
Our proxy will be used as Captive Portal integrated with Google Workspace, so we need to obtain a public TLS certificate for our proxy.
There are several free options to arrange such certificate from various providers, for example, Lets Encrypt but for the purpose of this tutorial it was easier to get one time certificate from ssls.
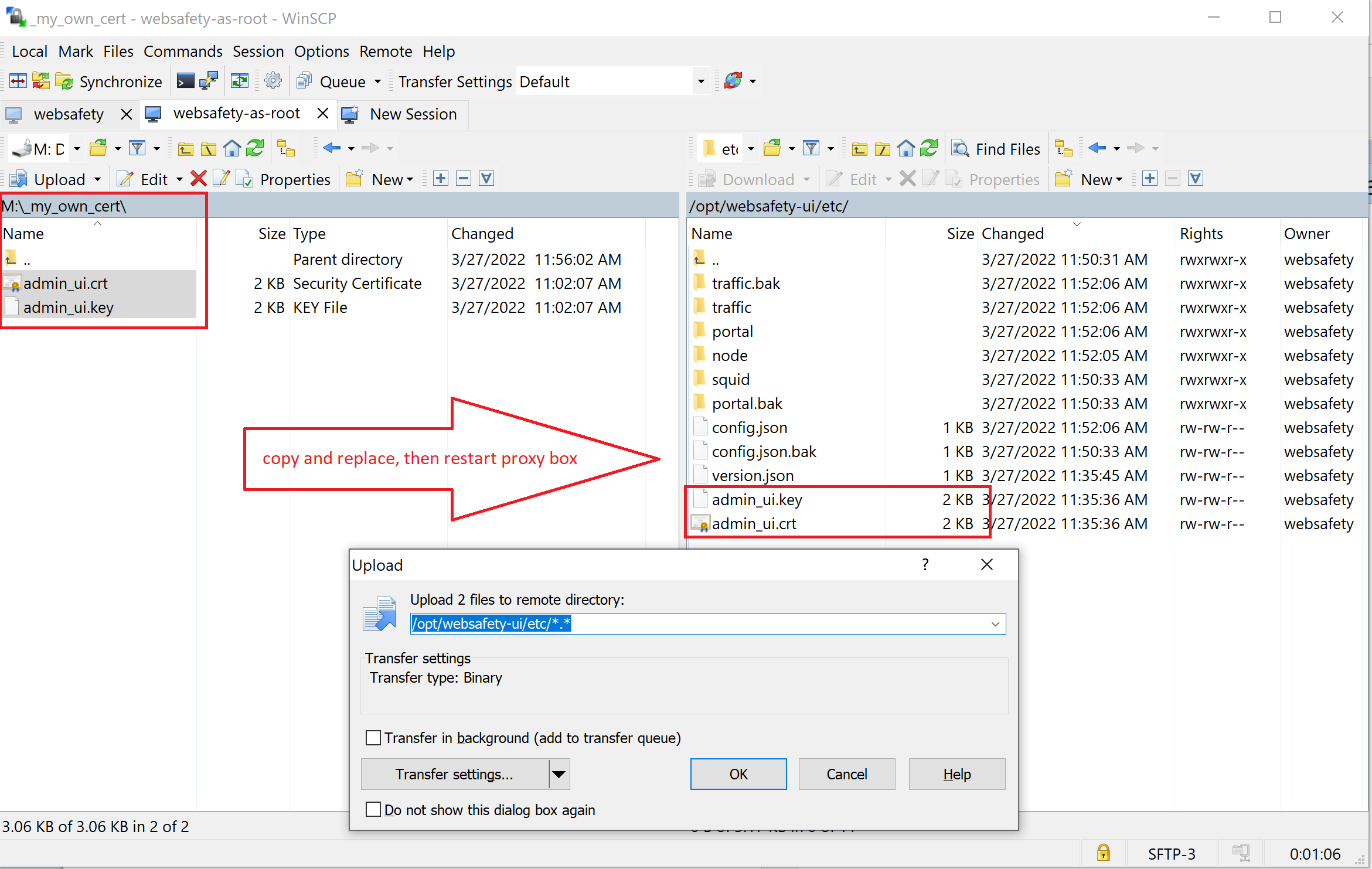
Save the certificate and private key as admin_ui.cer and admin_ui.key respectively (both PEM encoded) and upload them into /opt/websafety-ui/etc/ folder using for example WinSCP as shown on the following screenshot.
Restart the Apache web server on the proxy box with the following command or just reboot the proxy box from Azure portal.
systemctl restart apache2 && reboot
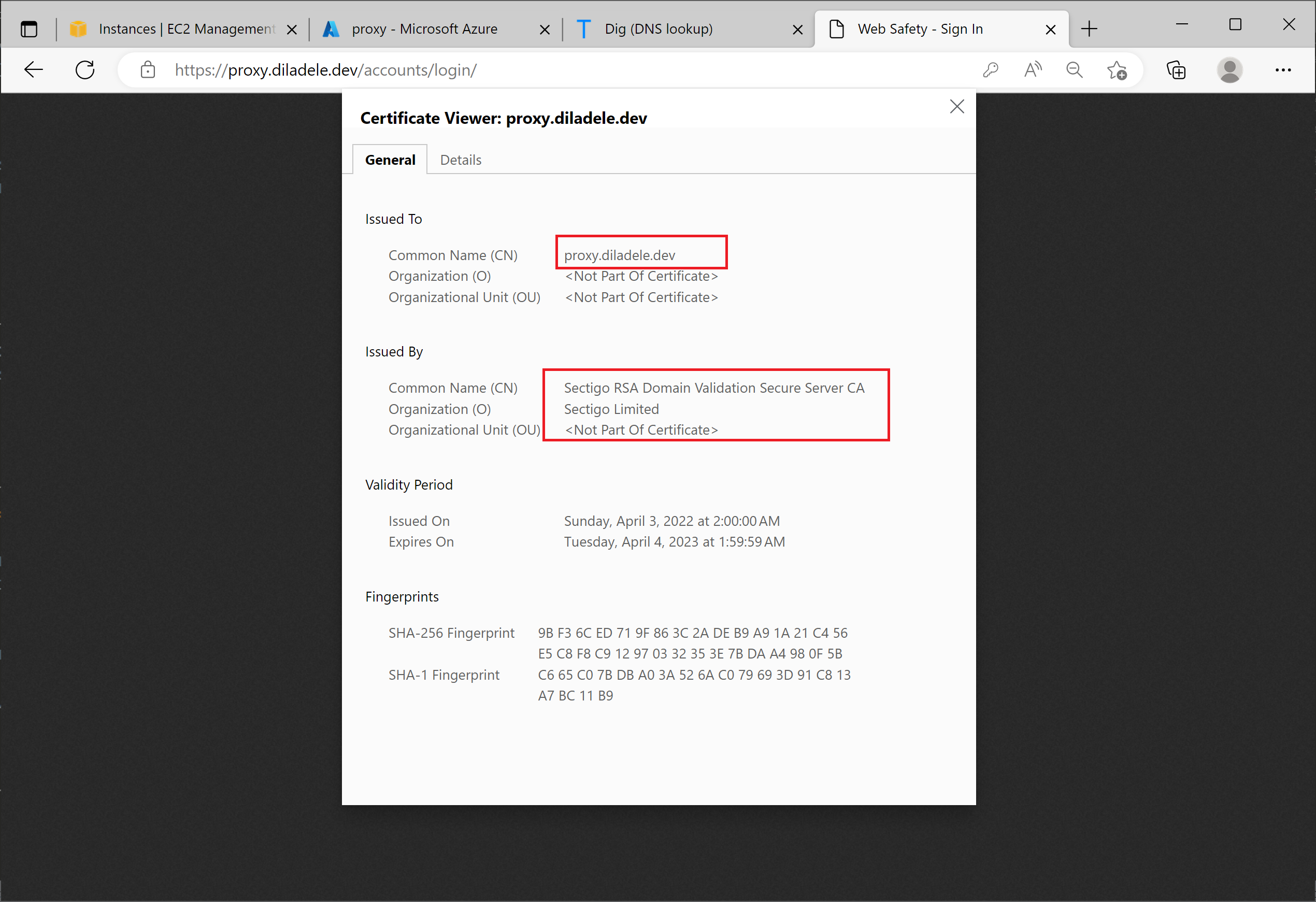
After that try connecting to the proxy box using https://proxy.diladele.dev URL (adjust the URL for your proxy box name of course). The connect should succeed without any warnings of a self-signed certificate present (default installation of Web Safety uses self signed certificate for Admin UI).
Setup HTTPS Inspection¶
In order for the Captive Portal to work correctly it is recommended to enable HTTPS inspection.
This step is recommended because by default browsers do not trust a Redirect to Captive Portal responses from the proxy. As almost all sites are using HTTPS nowadays having HTTPS decryption enabled is required for the browsers to start trusting such proxy redirections.
The following article explains what HTTPS decryption is, how it works and what steps are required to enable it - How It Works.