DNS Filtering Server¶
We will filter DNS requests within our LAN using Dns Safety filtering server.
Note
Dns Safety filter is a DNS forwarding server (like dnsmasq, unbound, pi-hole) with extensive filtering capabilities. It allows administrator to filter access to domain names by categories, easily block access to user specified domains and provide different filtering policies for different groups of machines in the local network. It is supposed to be deployed as primary DNS server in your local network and can forward DNS requests to your ISP’s DNS server, Google Public DNS, OpenDNS and other third party DNS providers. Internal DNS requests can be forwarded to internal DNS servers (for example Active Directory domain controllers).
The easiest way to deploy the Dns Safety is to download the virtual machine from https://dnssafety.diladele.com/download.html page and deploy it in a free VMware ESXi’s virtual infrastructure. Actually pfSense can also be deployed virtually in ESXi but we will not dive deep into this subject here.
We will need to configure the static IP address in Dns Safety UI. The idea is to have static IP address set to 10.0.0.2 with 255.255.255.0 netmask and gateway pointing to our pfSense firewall.
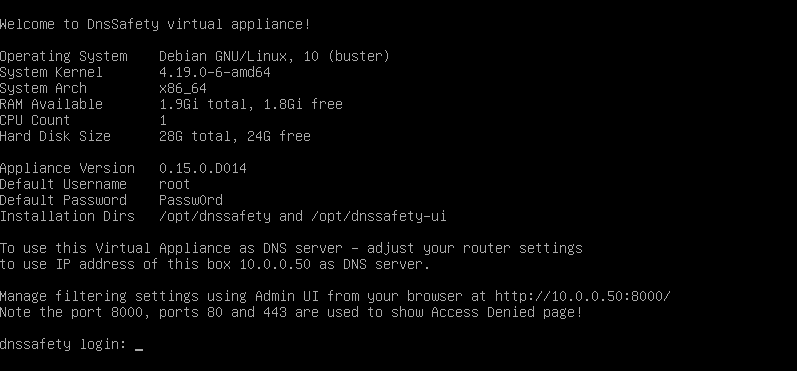
So navigate to the IP address for Dns Safety box shown in the terminal console, login using root and Passw0rd credentials, browse to Dashboard / Network Settings, configure them as shown on the following screenshot. After this is done, reboot the Dns Safety machine and try browsing the internet from your lan workstations - DNS requests shall be resolved normally and no errors shall occur.
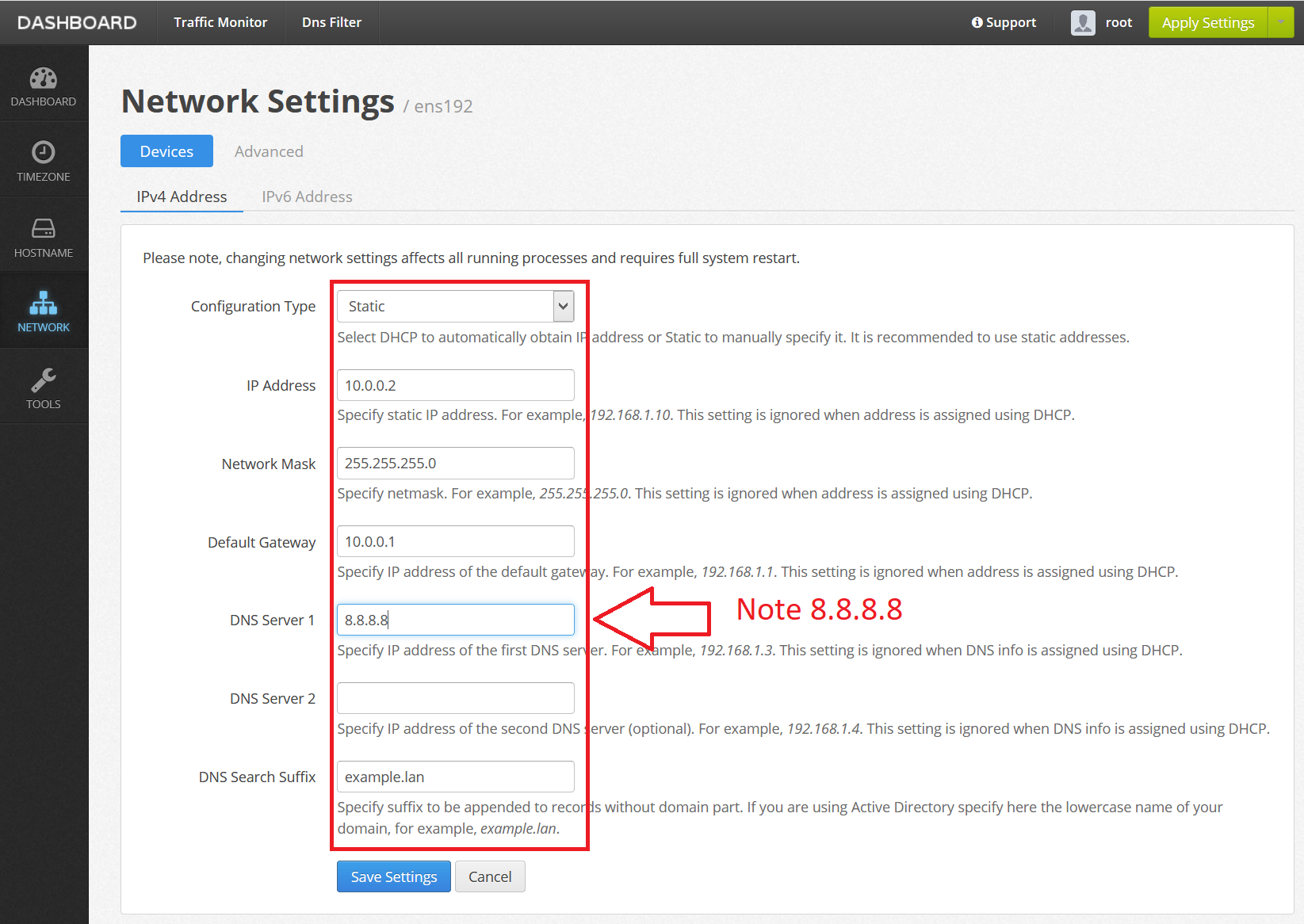
Note we are setting 8.8.8.8 as upstream DNS server for the Dns Safety machine itself. This is to prevent DNS recursion because Dns Safety loads this setting as upstream DNS server automatically and thus can talk to itself making a loop! Here you can also always put the IP address of your ISP providers DNS servers.
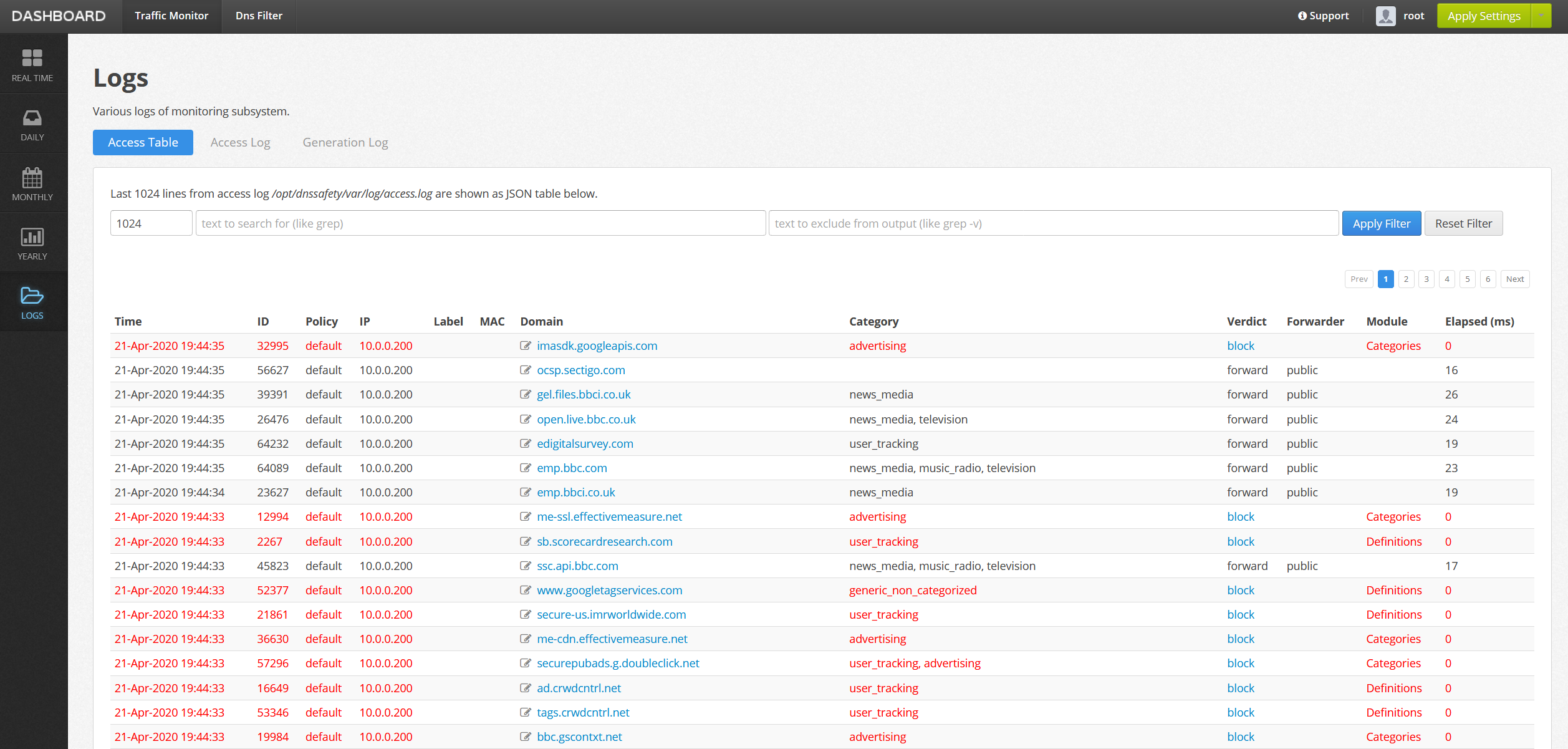
Intercepted DNS requests from LAN workstations will be shown in the Traffic Monitor / Logs page.
Dns Safety is a powerful tool and contains a lot of settings for filtering on the DNS level but our final goal is to be able to decrypt and filter HTTPS traffic so move on to the next step to deploy the explicit proxy and web filter in our network.