Check Squid Configuration¶
Warning
Please ensure your license key is not expired. If it is expired, Web Safety cannot start and ICAP connections from Squid will fail.
When Squid cannot connect to ICAP server it shows ICAP Connection Error page. If ICAP server is alive and running when this error occurs please check the following.
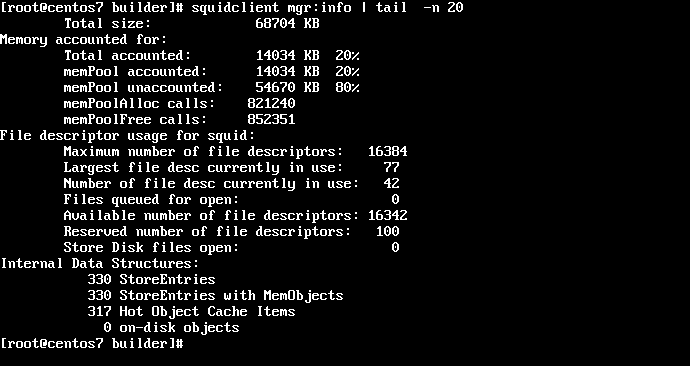
Ensure Squid has enough file descriptors available. Each ICAP connection takes at least one file descriptor and if there are a lot of ICAP connections being made then file descriptors may deplete faster than usual. The easiest way to check the FD limits is to run the squidclient mgr:info command as indicated on the following screenshot.
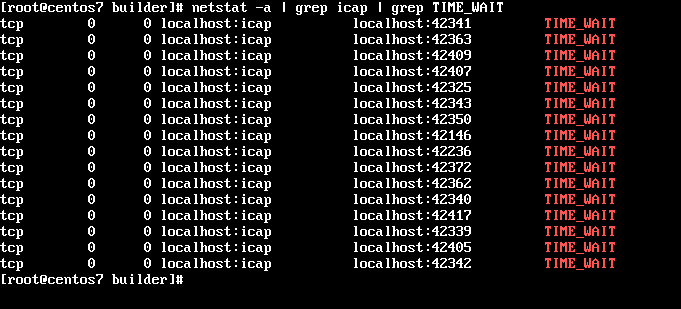
Check the number of connections to ICAP port 1344 in TIME_WAIT state. Currently Web Safety closes ICAP connection after it generates the blocked page so large number of connections in TIME_WAIT may indicate that too many sockets cannot be reused by Squid.
# netstat -a | grep icap | grep TIME_WAIT
Increase level of ICAP module debugging in Squid by adding
debug_options ALL,9to its configuration file, remove the /var/log/squid/cache.log and restart Squid daemon. From now on Squid will dump extensive info about ICAP transactions to log file and after ICAP error occurs again it may be possible to analyze what went wrong.
Please when contacting support@diladele.com with this error, dump as much information as possible about your networking configuration, including:
OS version you are using
Version of Squid and it compilation flags (type /usr/sbin/squid -v to get those)
Squid config file and firewall redirect rules if you are running it in “intercept” mode (invisible for browsers)
Squid logs (especially cache.log)
Version of Web Safety you are running, its logs and configuration files from /opt/websafety/etc
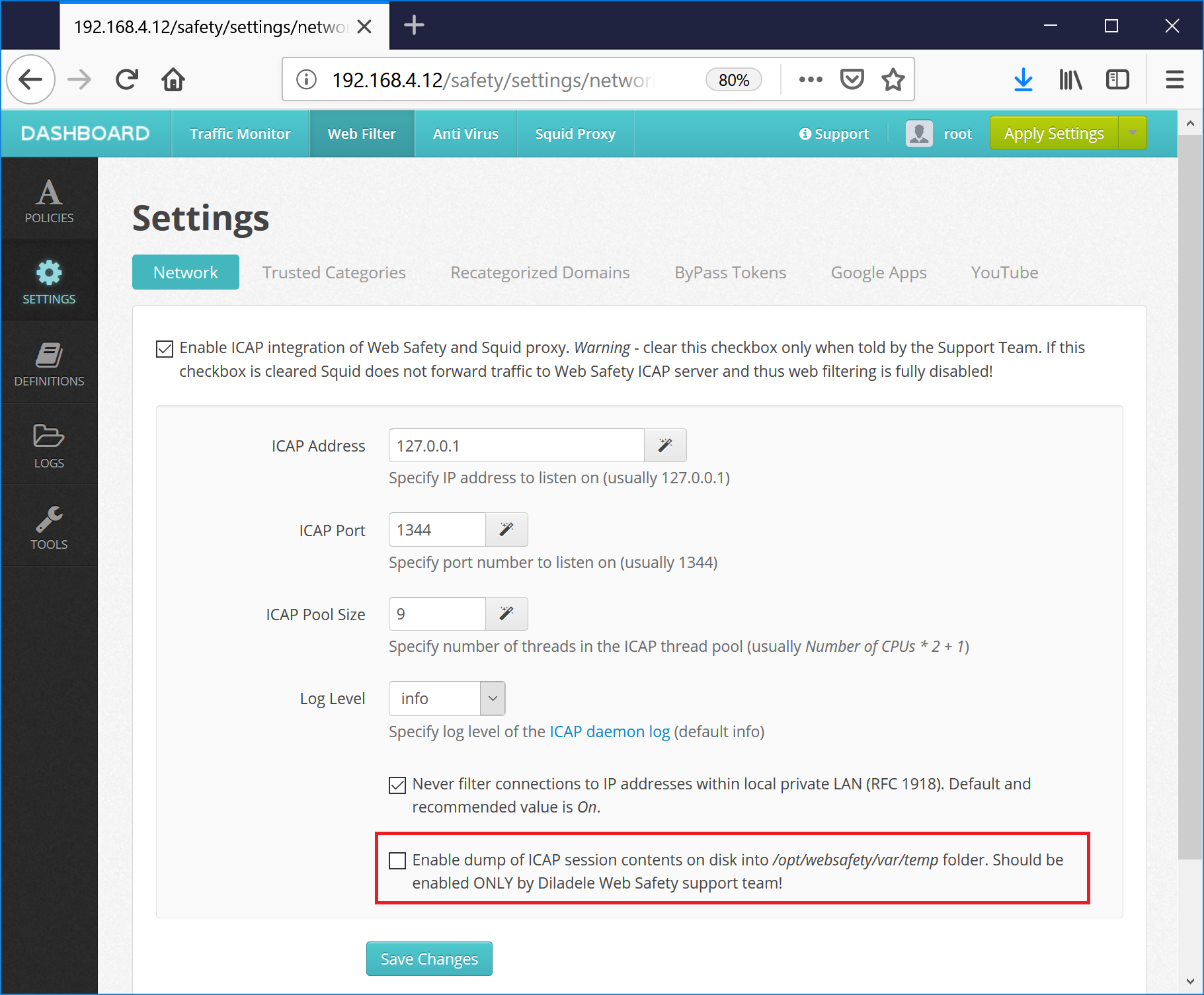
If possible it is also advised to do the dump of ICAP transactions between Squid and wsicapd. Go to UI / Web Filter / Settings / Network, check the ICAP Debug option, click “Save and Restart” button in the top right corner. Reproduce the error and pack *.sent and *.received files in /opt/websafety/var/temp folder - this may give us a better clue about HTTP/HTTPS traffic when error occured.