HTTPS Filtering on Windows 10 with Squid and Docker¶
Note
We now have a new project - Web Filtering Proxy for Microsoft Windows. It combines best features of Web Safety but runs natively on Windows. No need to use Hyper-V or dive into Linux specifics. You can enable proxy authentication, HTTPS decryption and filtering with several mouse clicks from Microsoft Management Console. See https://webproxy.diladele.com/.
Foreword¶
In this tutorial we show how you can easily enable efficient and fast web filtering of your network at your home, school or company if you have a machine that runs Microsoft Windows 10 (Professional, Enterprise or Education)/Windows Server 16.
Note
If the license in the product has expired, please request one at support@diladele.com.
Overview¶
To enable filtering of HTTP traffic in the network, we will use Squid Proxy Server and Web Safety ICAP web filter.
Squid is an open source and well-known web caching proxy server that supports different protocols including HTTP, HTTPS and FTP. It helps reducing bandwidth by caching most frequently requested web pages and provides functionality for extensive access controls and content adaptation. Even though Squid is mostly supported for Unix platforms, its recent versions also support Windows.
Web Safety for Squid Proxy is an ICAP web filtering server that integrates with Squid Proxy and provides rich content filtering functionality to sanitize Internet traffic passing into internal home/enterprise network. It may be used to block illegal or potentially malicious file downloads, remove annoying advertisements, prevent access to various categories of web sites and block resources with explicit/adult content.
The underlying platform that allows us to run Squid on Windows is Docker. It enables easy and self-contained build and deployment of applications on different operating systems. You can read more about it on the official Docker site (https://docker.com).
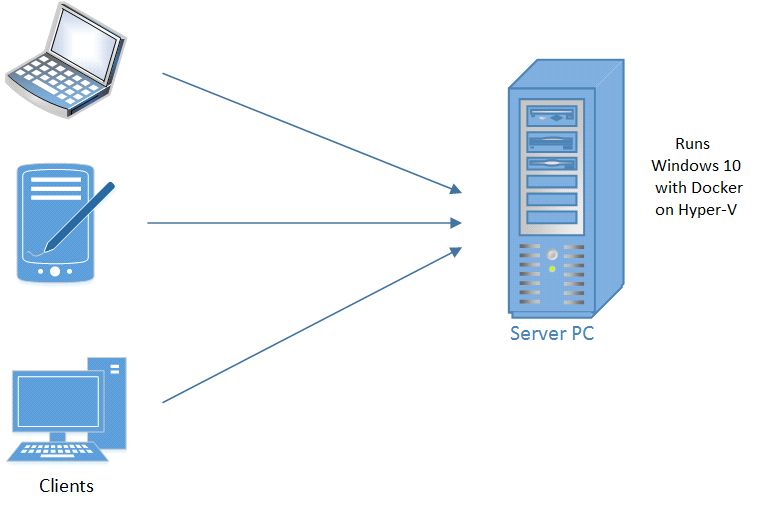
Our network setup is depicted in the figure below. We will setup an explicit filtering proxy on the PC with Windows 10 and redirect client browsers on all devices in the local network to use this PC as a proxy in order to access the Internet. We will filter both HTTP and HTTPS traffic.
How to configure filtering proxy¶
Prerequisites. Currently, Docker supports only 64 bit version of Windows 10 (Professional, Enterprise or Education editions). So we expect this operating system to be installed on the server PC. You also need connection to the Internet.
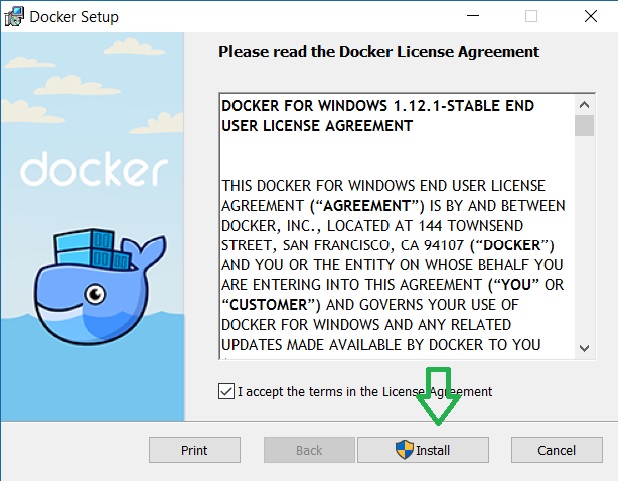
Step 1. First of all, we need to install Docker. Go to the Docker web site and download Docker for Windows
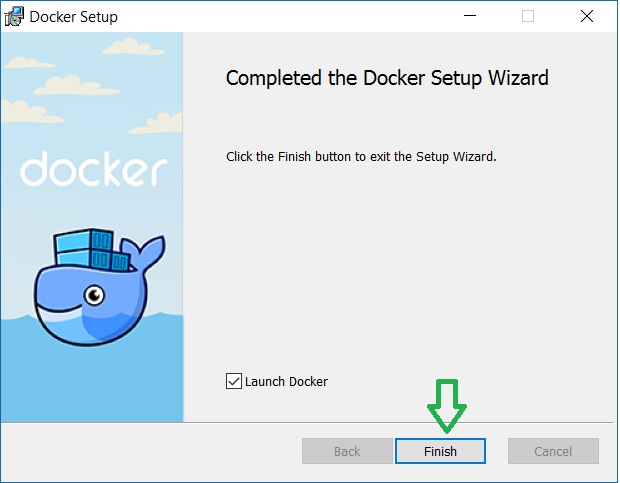
Step 2. Run the executable and click Next or Ok till the docker is installed:
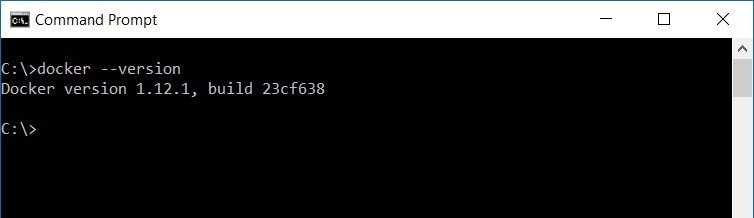
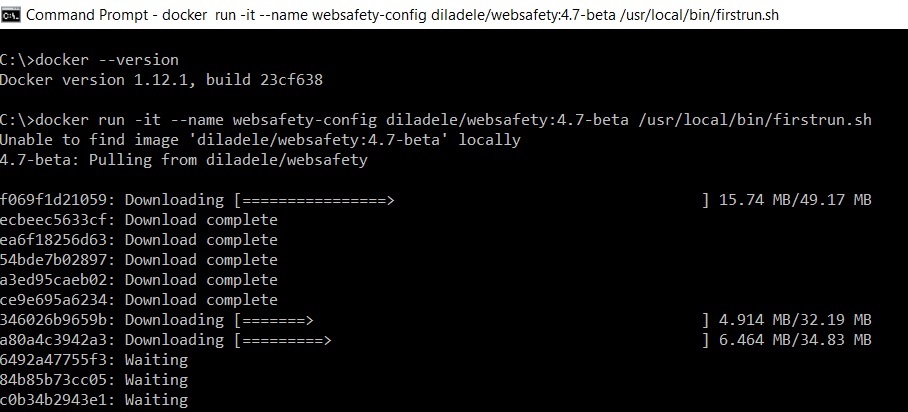
Step 3. After docker install, please open a command console (i.e. by typing cmd in the Windows search box and pressing Enter). If Docker is installed correctly, typeing docker --version should output something like this:
Step 4. In order to pull the docker image with installed Squid and Web Safety type the command below and hit Enter.
docker run -it --name websafety-config diladele/websafety:6.1 /usr/local/bin/firstrun.sh
This will start pulling all necessary images to your machine and set up the proper configuration for the container (this can take some time).
After that, start the container in the background mode with the following command. It will launch Squid on port 3128 and the Web UI on port 8000.
docker run -dt --name websafety --volumes-from websafety-config --dns=8.8.8.8 -p 8000:80 -p 3128:3128 diladele/websafety:6.1
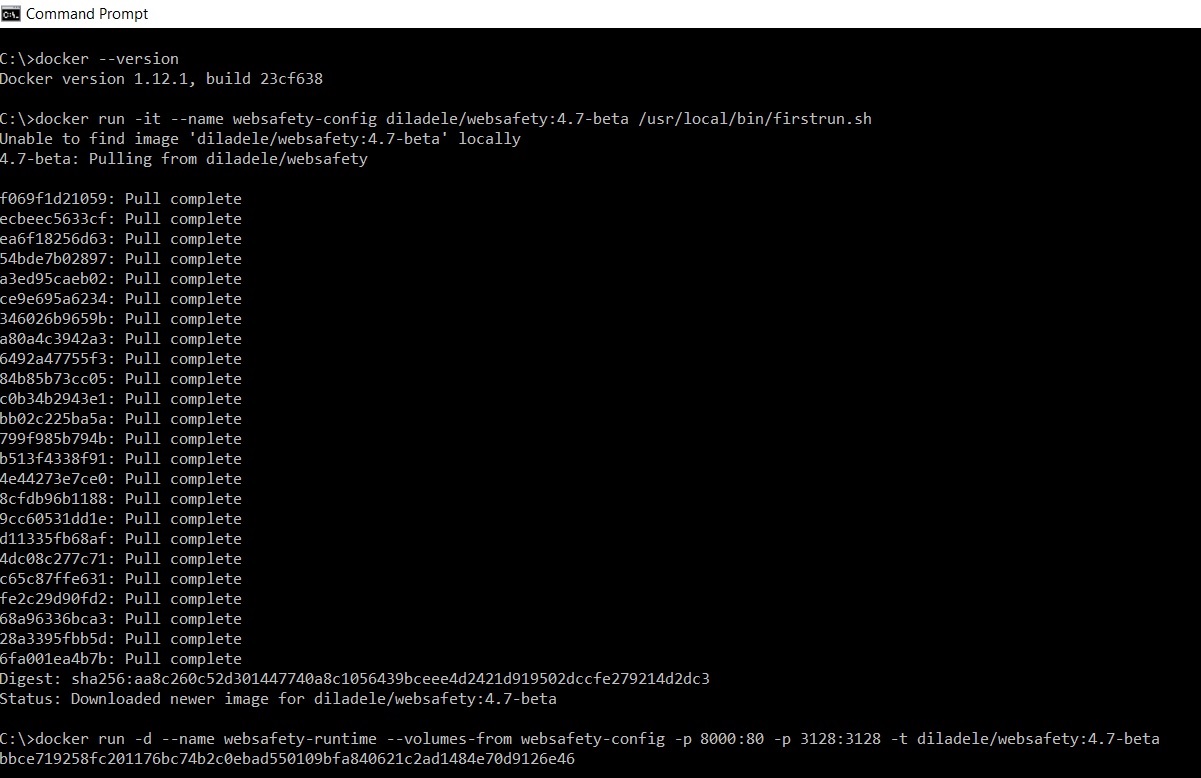
(If you know your DNS servers, i.e. using ipconfig /all command, you can use them instead of 8.8.8.8).
Now you have your server running.
Note
At any moment you can stop the running container using docker stop websafety or start it with docker start websafety. In order to remove the container, use docker rm -v websafety.
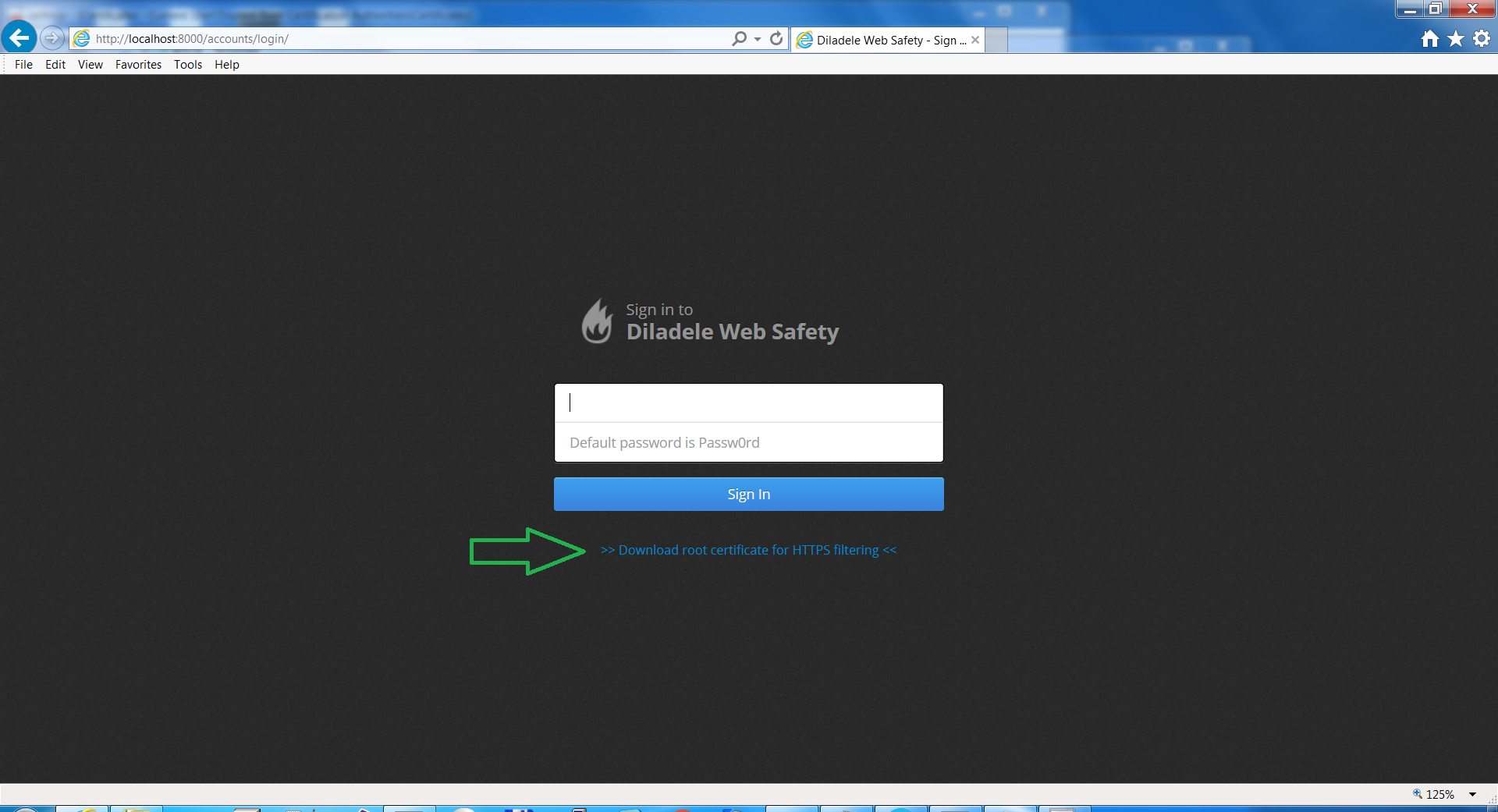
Step 5. Open Internet Explorer or some other browser and go to http://localhost:8000
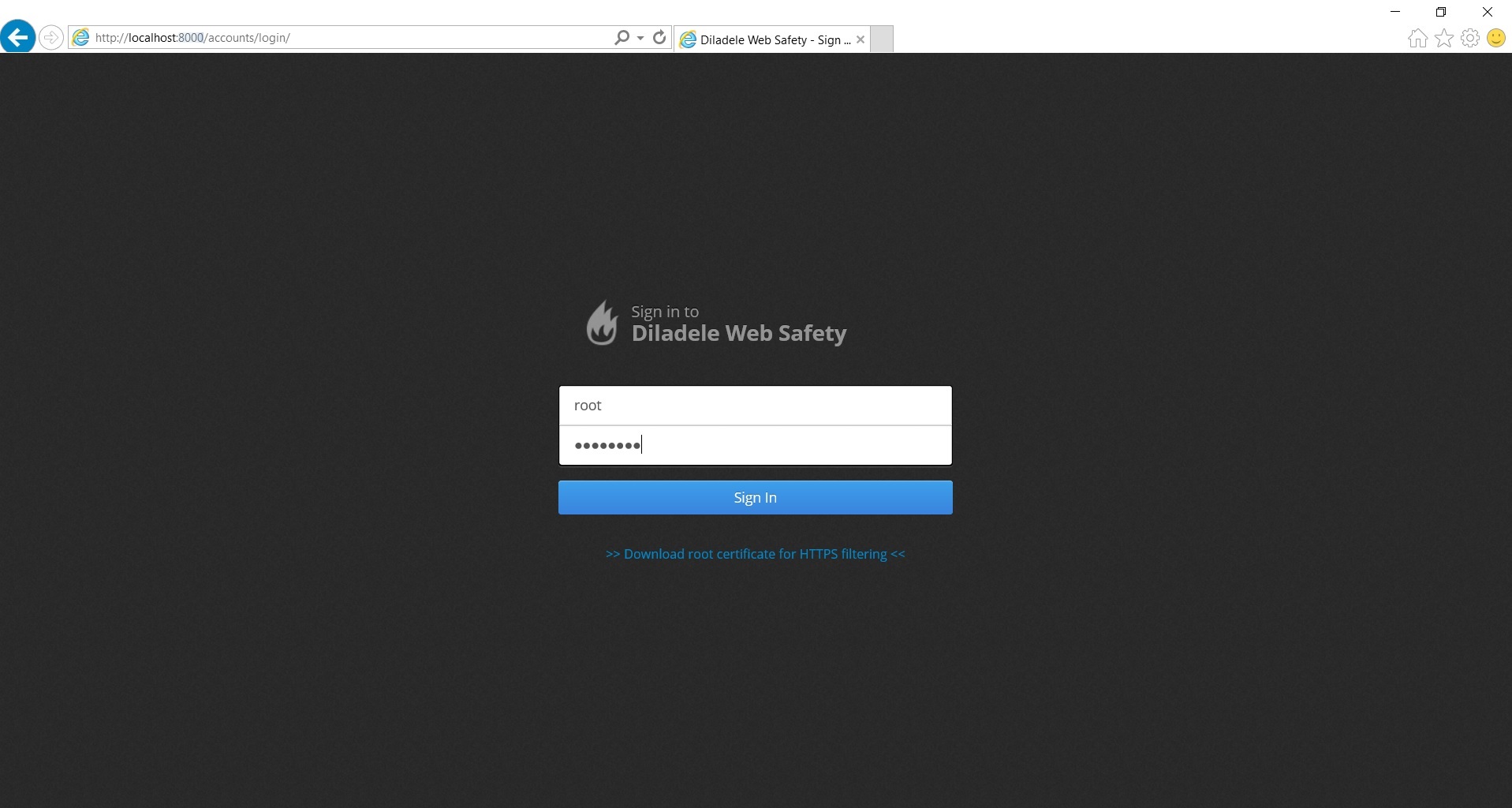
You should be presented with Web Safety Web UI. Put root as login and Passw0rd as password (please notice zero, not O in the password). Check that dashboard does not have any errors.
You can use this console to configure your filtering rules and all types of policies. For more information please see Administrators Guide 9.1 (Stable).
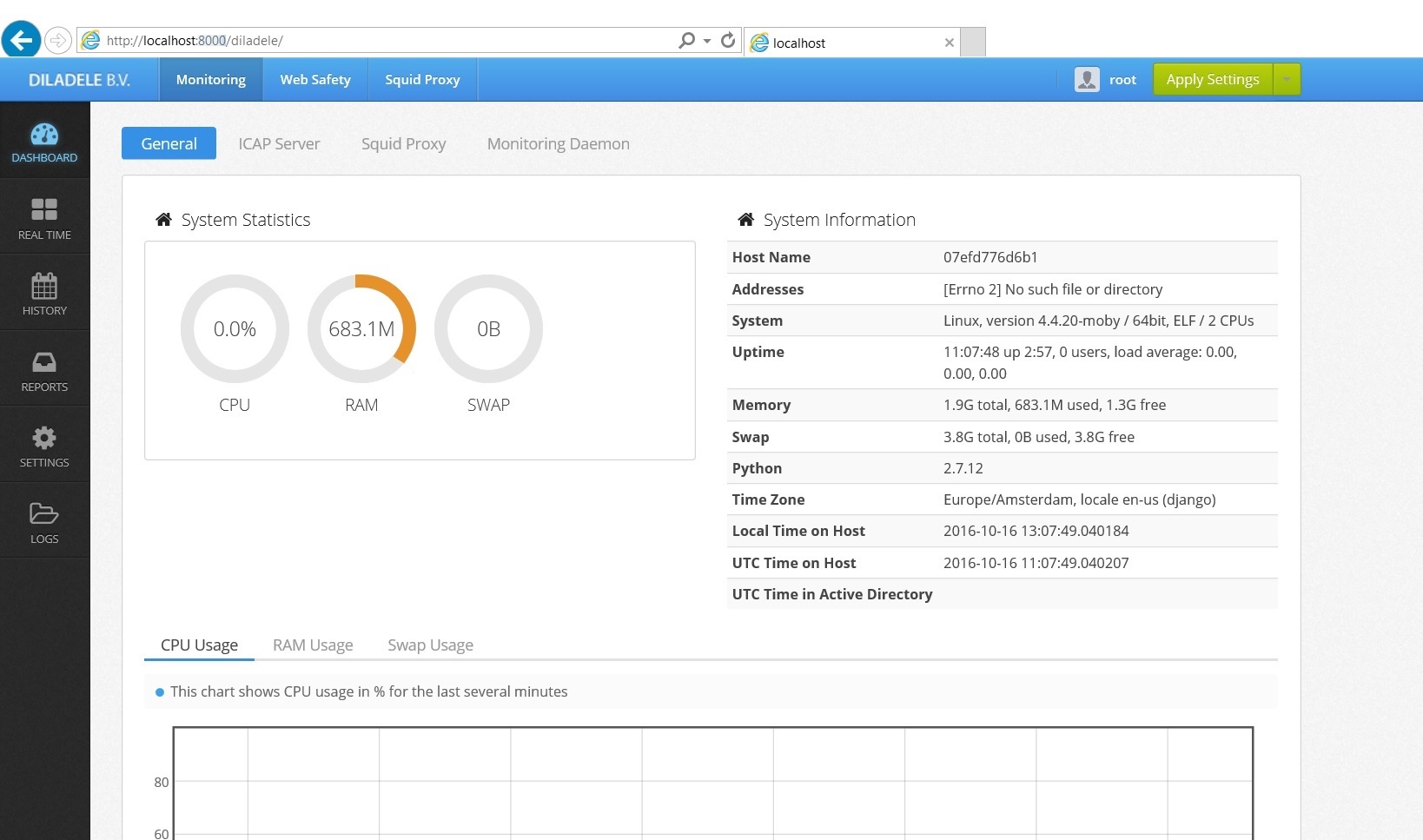
We recommend changing the administrator password immediately.
How to configure client browsers¶
Now we need to configure the clients. For that we have to know the IP address of the server, where Squid and Web Safety are running.
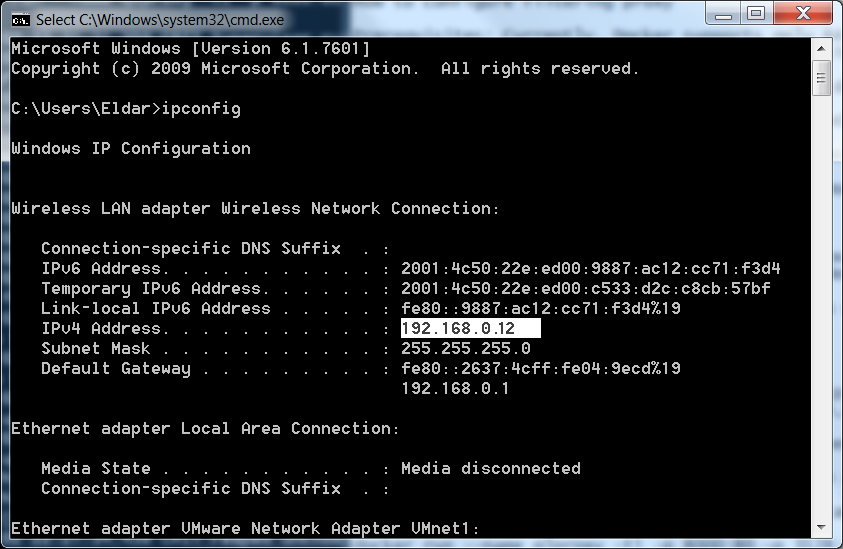
On your server, please open the command line (Start->Type cmd.exe in the search box and hit Enter) and type ipconfig. This should give you the IP address of your Windows host machine that we need to specify in the client browsers (in my case it is 192.168.0.12).
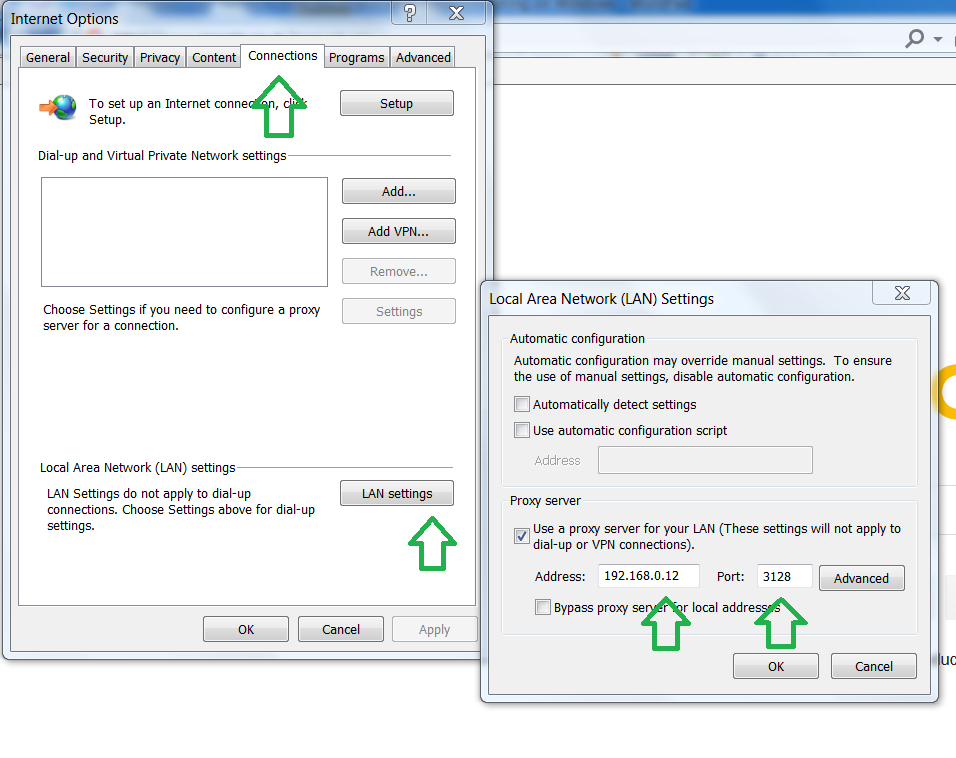
On the client machine open Internet Explorer (or any browser you use) and set the proxy to the server IP address and port to 3128.
Note
Please make sure, the firewall on your Windows Pro server machine should have a rule to allow incoming traffic on port 3128!
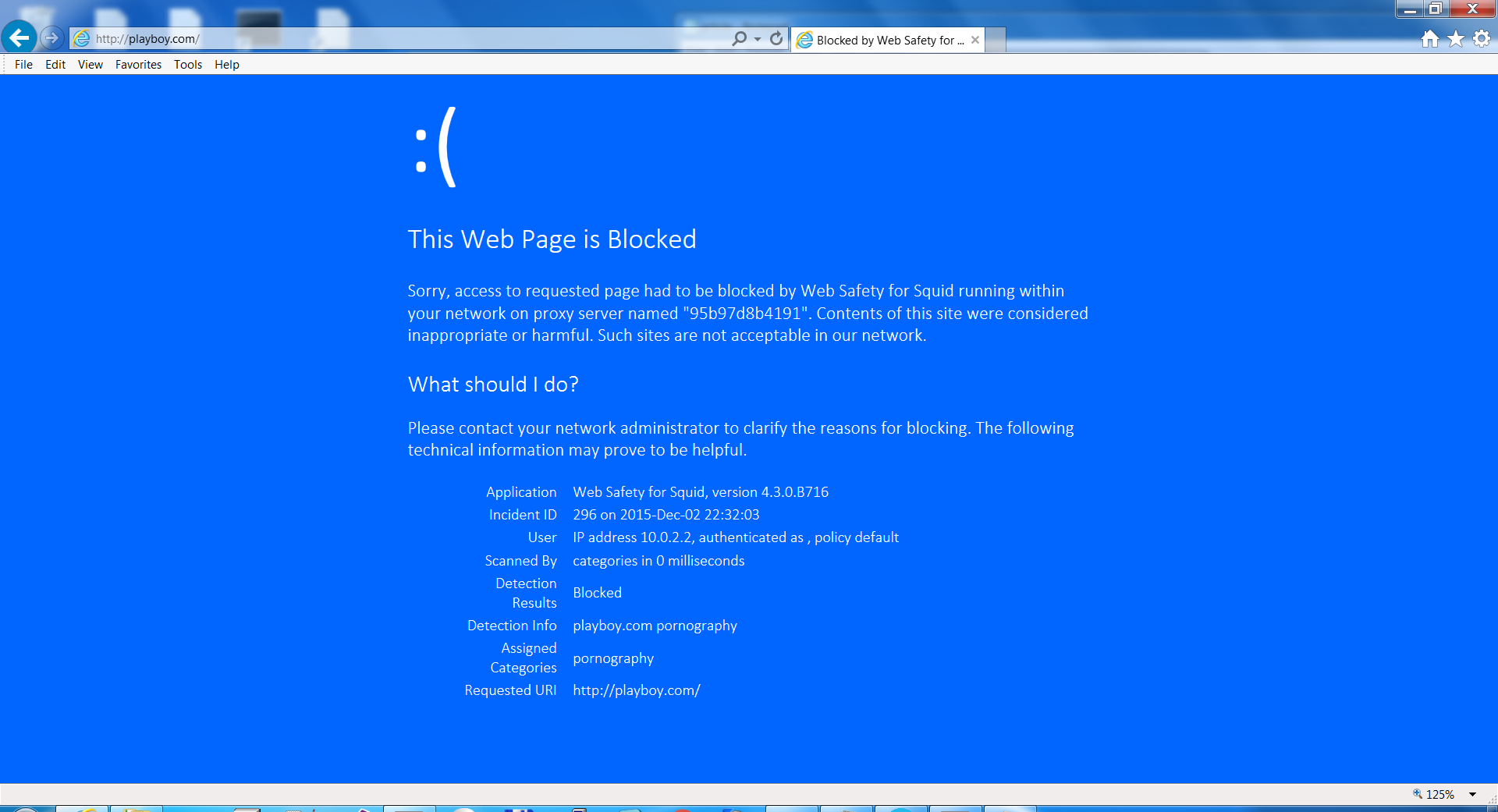
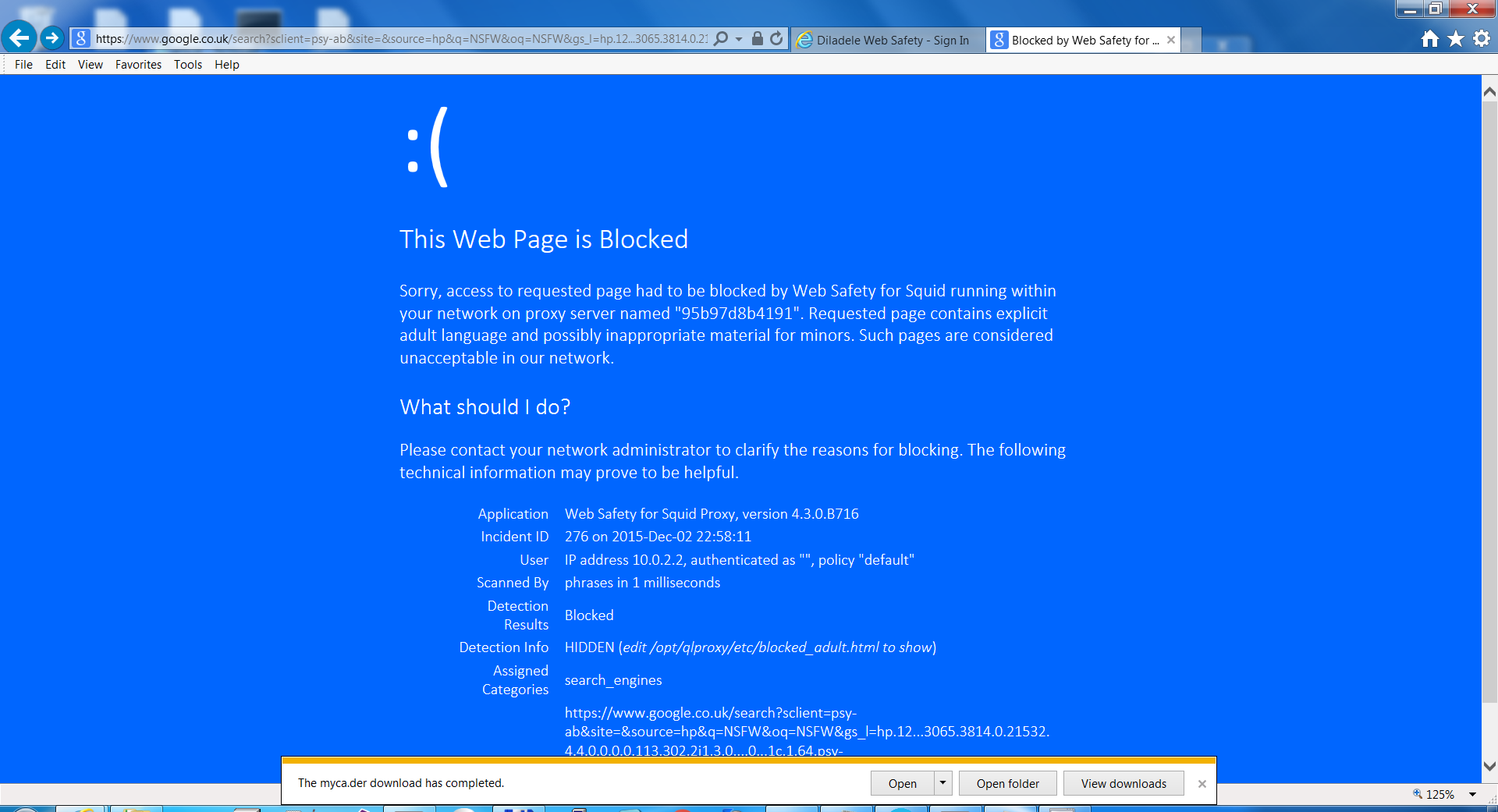
Now if you try to access some website with adult content, you should see a blocking page:
Configuring HTTPS filtering¶
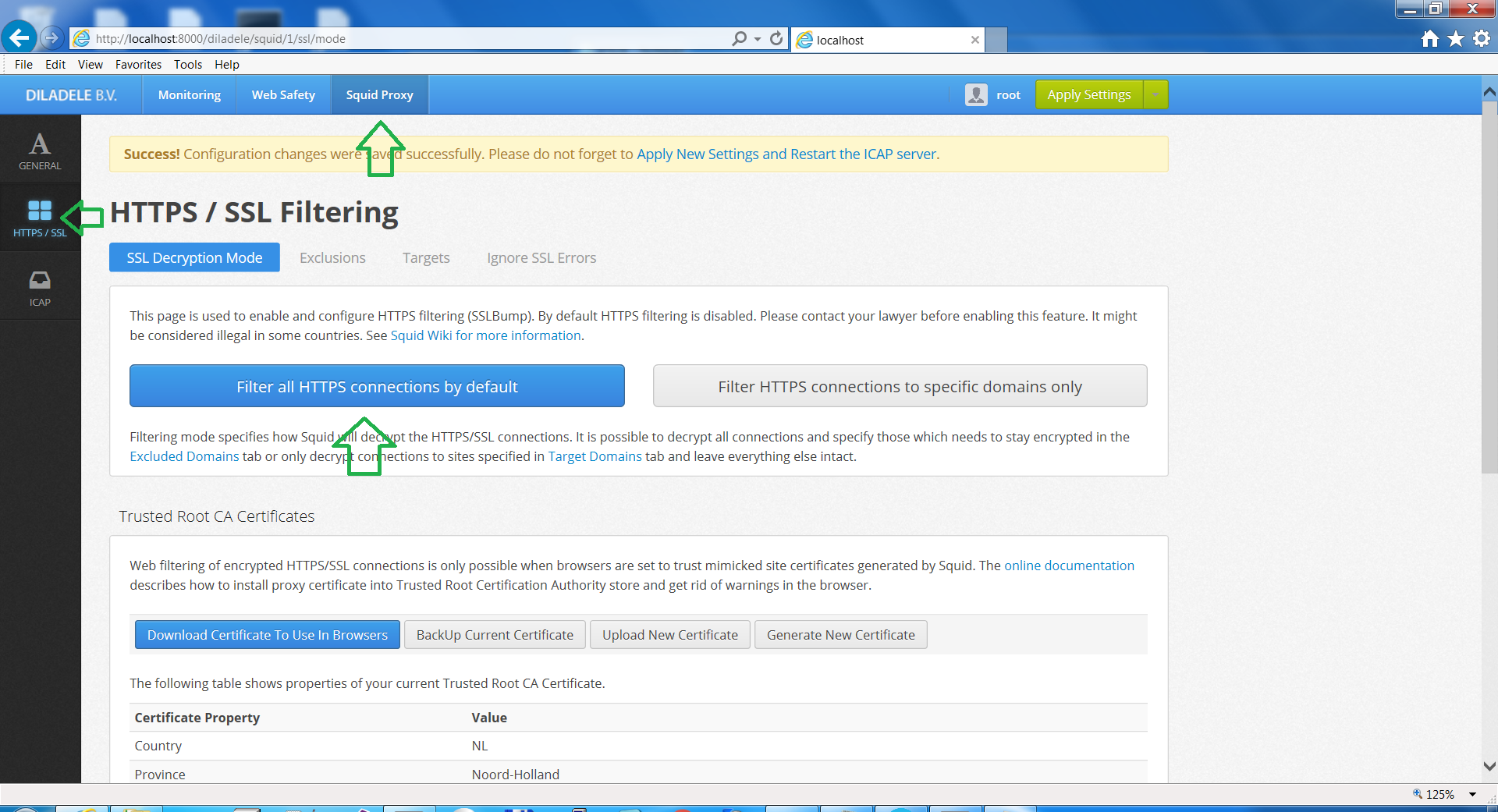
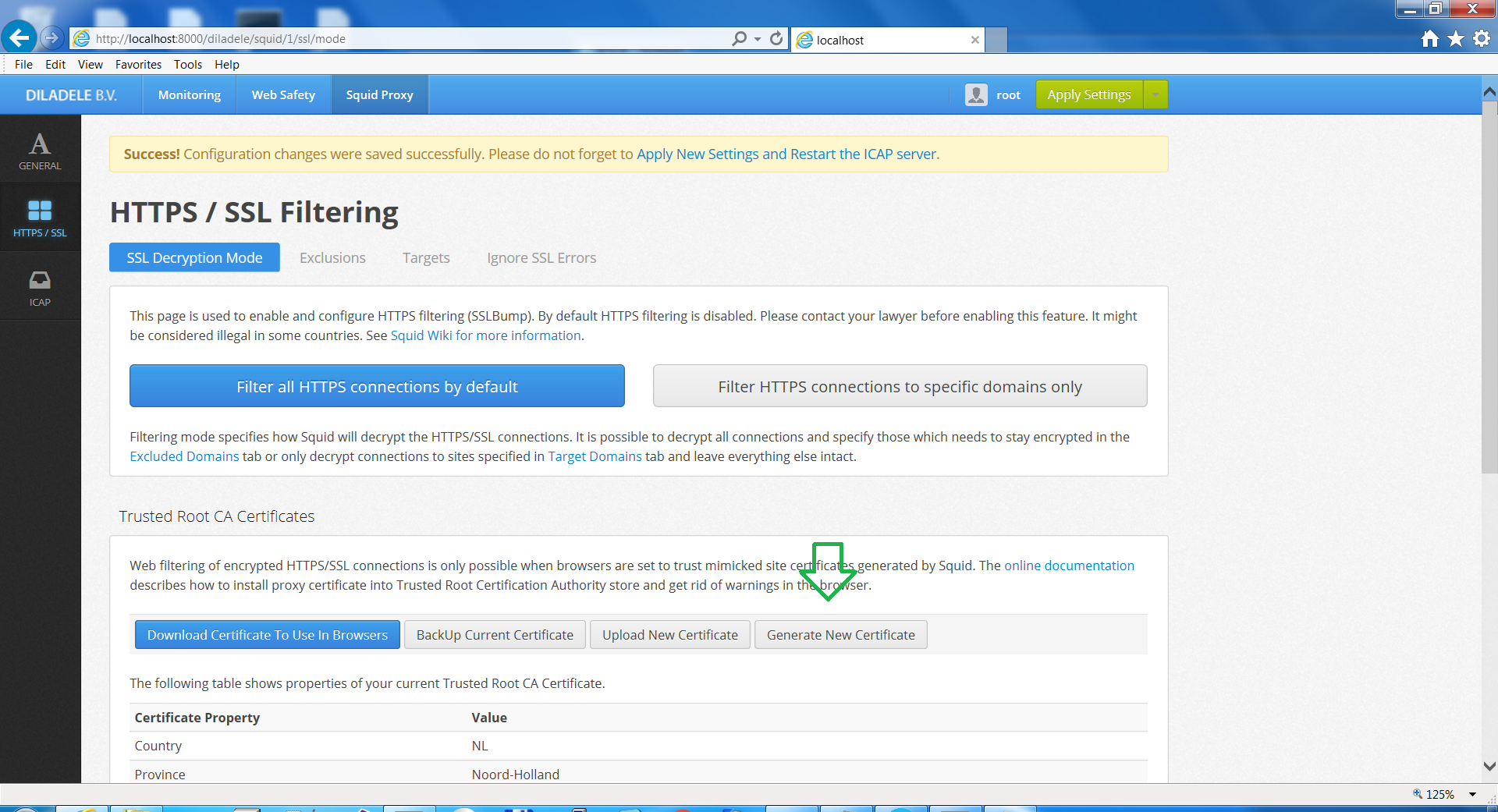
In order to enable HTTPS filtering (i.e. for Google Safe Search, YouTube, Facebook), please go to Web Safety Web UI, then Squid Proxy (right top), HTTPS/SSL (left panel) and click “Filter all HTTPS connections by default”:
Click “Generate new certificate”, fill in your data and press “Generate Certificate” button. This will generate a self-signed certificate that can be used by the clients in order to use HTTPS without warnings.
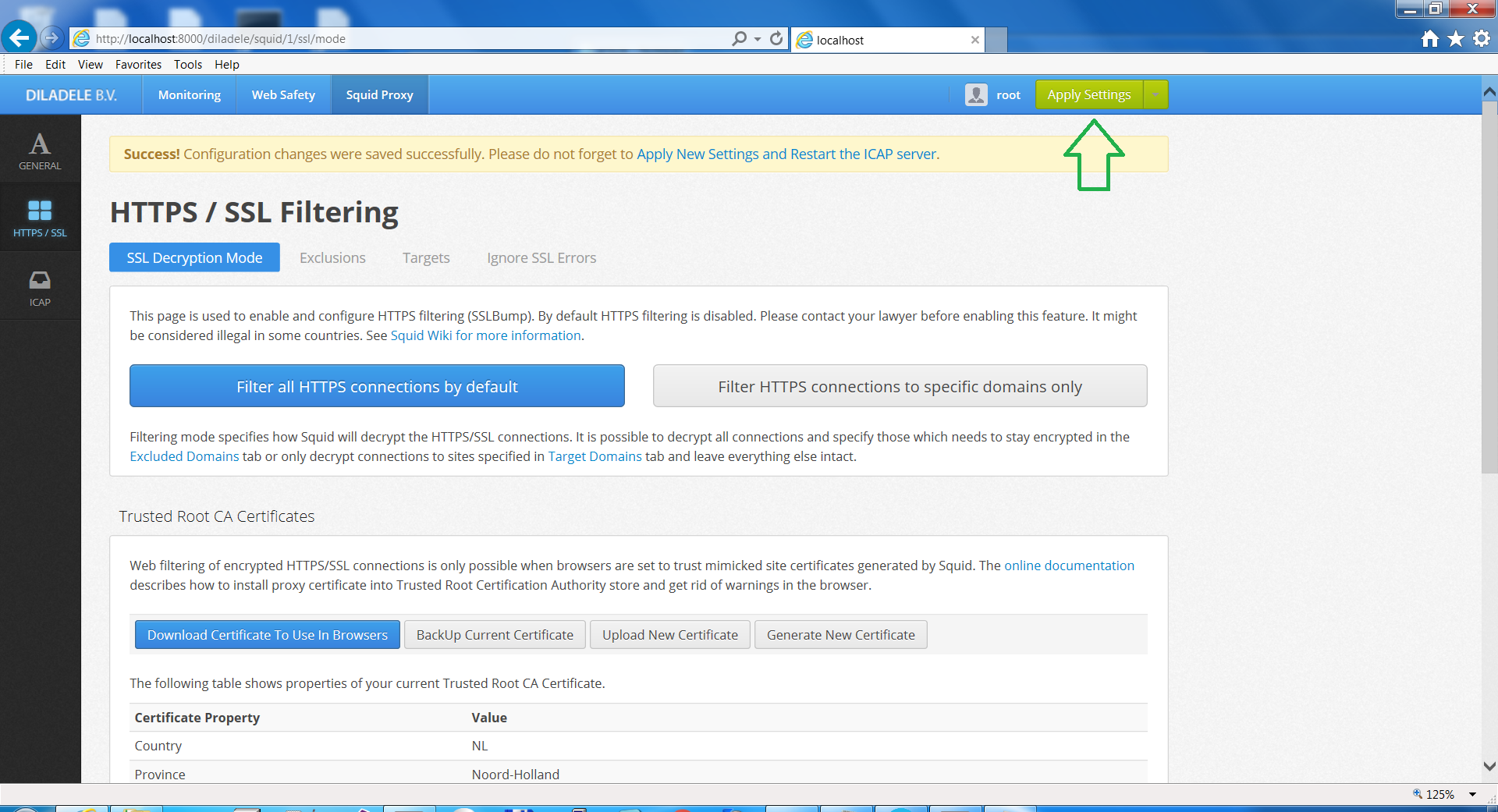
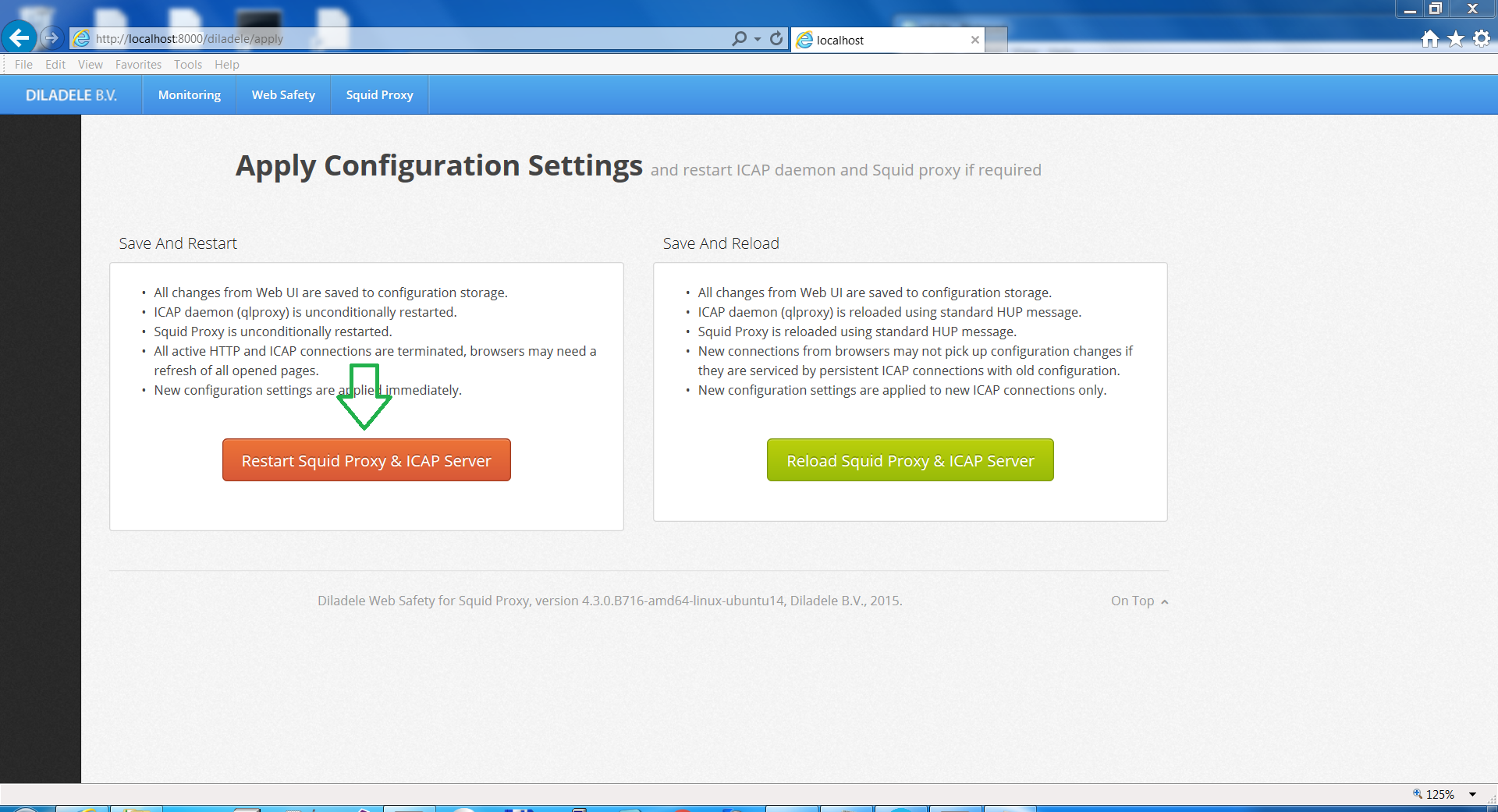
Then click “Apply New Settings and Restart ICAP Service”:
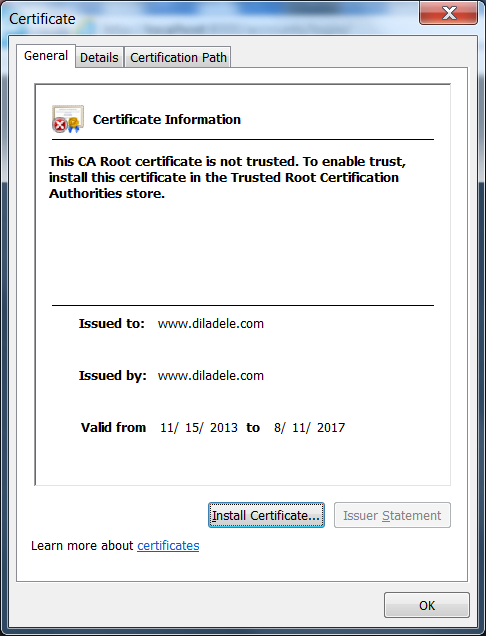
If you try opening Google on the client machine you will see a warning that certificate is not trusted (you can read how HTTPS filtering works in more detail here - HTTPS Filtering.
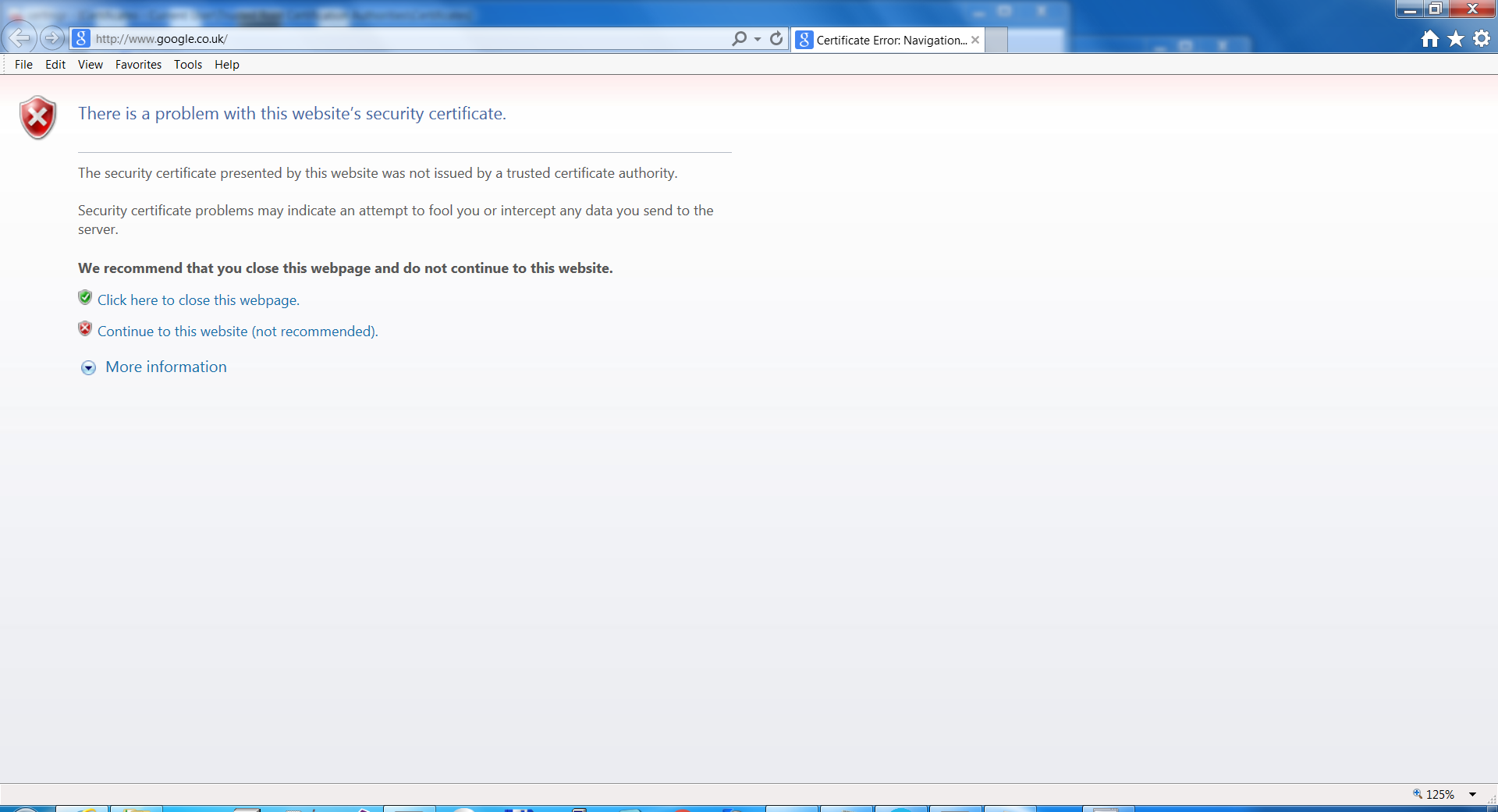
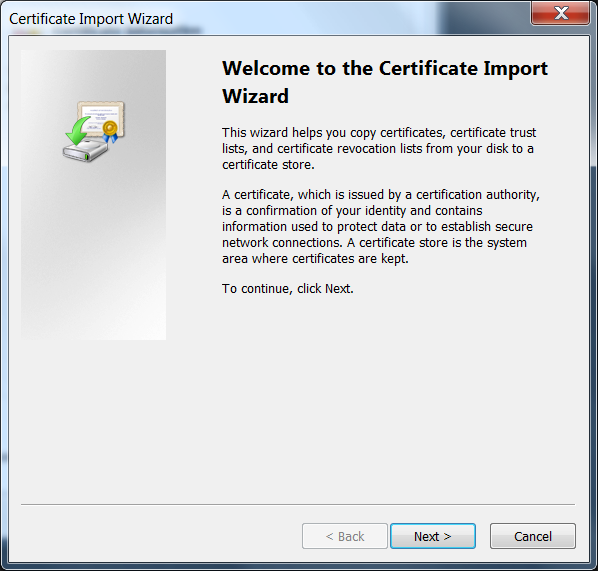
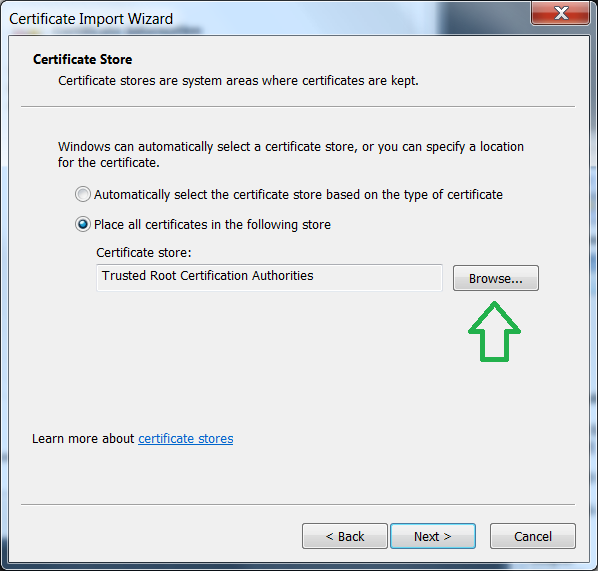
To get rid of it, we have to install our generated certificate on the client machine. Go to the Web Safety Web UI and download the certificate.
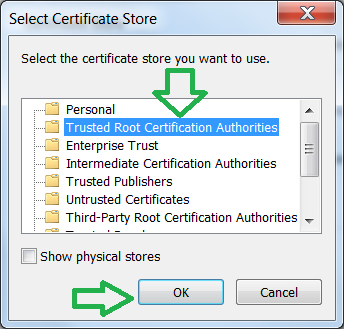
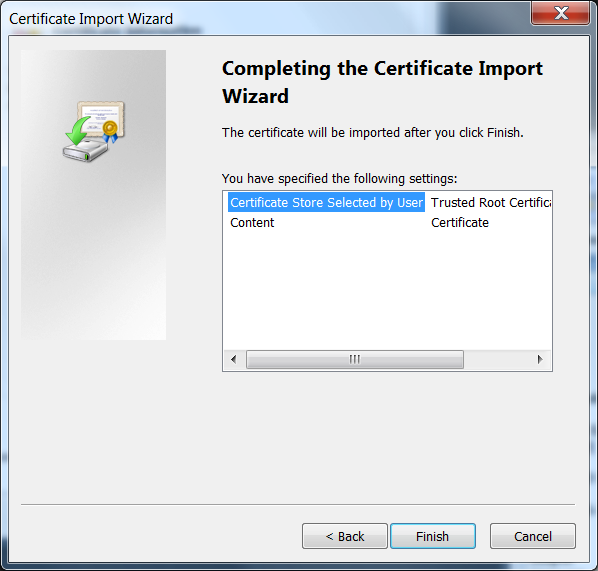
Double click it and install in the Trusted Certificate Store:
Now if you go to google there should be no warnings. Try searching for NSFW term - it should be blocked and lead to the following page:
Conclusion¶
So we successfully enabled filtering of HTTP and HTTPS on the local network.
Notes¶
If Squid blocks your access to port 3128 - you should add your network to the /etc/squid/squid.conf or check your firewall settings.
If your browsing is slow, there could be a problem with DNS. Run docker exec -it websafety /bin/bash and see what is in /etc/resolv.conf. You can try specifying your local DNS or Google public one 8.8.8.8.